How to stop ubuntu from collecting data about your pc
Ubuntu collects information from your system including hardware and software and sends them to Ubuntu servers. The data includes the information about the packages you have installed, how you are using it, and the applications crash reports. It also generates reports related to generic hardware related information like upgrades, processor architecture, installed memory, screen resolution and much more. However, one thing to note that Ubuntu does not collect IP address information.
The purpose of Ubuntu behind collecting this data is to build a better understanding of what applications are being installed and used mostly so that they can keep their focus on the areas people care about.
However, if you do not want your data to be sent to online servers, you can force Ubuntu to stop collecting data from your PC. In this article, we will see what kind of data Ubuntu collects from our PC and how to stop it.
Nature of data Ubuntu Collects
- System information report
- Packages information
- Crash reports
I will use Ubuntu 18.04 LTS OS for describing the procedure mentioned in this article to stop Ubuntu to collect and send data to Ubuntu servers.
1. System information report
- Ubuntu flavour
- Ubuntu version
- Network connectivity or not
- CPU family
- RAM
- Disk(s) size
- Screen(s) information
- GPU information
- CPU information
- OEM Manufacturer
- Location (that was set during installation)
- Installation duration (time taken)
- Auto login enabled or not
- Disk layout selected
- Third party software selected or not
- Download updates during install or not
- LivePatch information
- BIOS info
- Device model
- Partition
- Time zone
You can also view yourself the information that is sent to Ubuntu servers by running the following command in Terminal:
Stop sending system reports
You can opt out of this information collection by Ubuntu. At the first boot after a new installation, you will see the following screen after a welcome screen. Here in the following screen there is the option, asking you to send this information to Canonical or not. Choose the radio button that says No, do not send system info.
If you did not select this option first time after installation, you can also opt-out of this option later. Run the following command in Terminal to opt-out of sending system information report to Ubuntu server:
2. Packages information
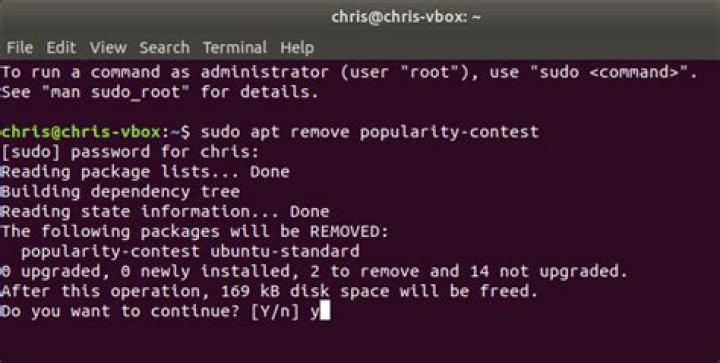
Ubuntu includes an optional tool Popcon or popularity contest that collects information about most frequently installed packages and send them back to the distributions so that they can accordingly prioritize and focus their resources. This information can also be useful to system users who can acquire software recommendation from other distribution users. However, Popcon only sends information for packages installed through Debian packages, not for packages installed through other means like flatpak, snap, etc.
Stop sending packages information report
You can avoid this data collection from Ubuntu. For this, you have to opt-out of the package popularity contest by editing /etc/popularity-contest.conf in any text editor and altering the value of PARTICIPATE to no.
Run the following command in terminal to edit popularity-contest.conf file using nano editor:
You can use any other text editor for this purpose.
When the file opens, find and change the value of “PARTICIPATE” to “no” as shown in the below image.
By doing this, you will be opted out of the popularity contest and it will no longer send the packages information to Ubuntu.
3. Crash reports
Ubuntu includes an Apport tool that is configured to automatically detect application crashes and send crash reports to Ubuntu server without user interruption. These reports are used by application developers to understand and identify what are the issues and bugs in the application and why they are occurring. However, you can also opt-out of this automatic crash report.
Stop sending Crash reports
Click on the upper right corner arrow on your Ubuntu desktop and from the menu that appears, click on the Settings icon.
For a clear understanding, see the below image.
It will launch the settings window. On the left pane, click on Privacy. Then from the corresponding right pane, click on Problem Reporting option.
Click on the toggle Send error reports to Canonical to turn it to off position.
After doing this, Apport will still generate the crash reports but will ask for your approval before sending them.
Any user, who do not want to send their system information including their hardware and software information, installed packages information and their application crash reports to Ubuntu server can easily do that by following the above-described method.
Karim Buzdar
About the Author: Karim Buzdar holds a degree in telecommunication engineering and holds several sysadmin certifications. As an IT engineer and technical author, he writes for various web sites. You can reach Karim on LinkedIn
Thanks to the doors-wide-open nature of open-source software developers it’s very easy for you to find out.
It also helps that Canonical is being (unusually) upfront and open about the Ubuntu data collection policy, which I should add is entirely opt-out for new Ubuntu 18.04 installs, and opt-in on upgrades.
Whether you plan on making the upgrade to 18.04, or you already have (but whizzed through the Ubuntu Welcome screens without paying attention) read on to see what data Ubuntu collects, collates, and couriers back to Canonical.
Ubuntu Data Collection in 18.04+
Ubuntu 18.04 includes a data collection tool called ‘Ubuntu Report’ – but what does it do?
Sorry, what?!
We were the first to report on Ubuntu’s plans to gather system metrics in new installs of 18.04 LTS onwards.
And I’ll be honest: when I first heard about the plan (surreptitiously via a code commit, in case you’re curious) I was a little worried.
Memories of the Ubuntu ‘Spyware’ debacle still linger in people’s minds
Worried not for Canonical and its plans but for the reaction the plans will generate among its (seemingly many) critics.
So when Canonical did go public with its wont to collect system data on new and existing Ubuntu installs a fair bit of, let’s say ‘consternation’ greeted the news.
Memories of the “Ubuntu Spyware” debacle still linger in people’s minds.
But it’s not fair; the anodyne Ubuntu Report tool in Ubuntu 18.04 is as far removed from the aforementioned meta-data munching mis-step as possible.
Unlike the Unity Dash the Ubuntu Report tool isn’t some privacy-invading tentacle looking to grope your system search habits for the purpose of serving you pointless shopping suggestions.
The reality is actually pretty boring.
Thankfully for my nerves (and no doubt the bods over at Canonical HQ) the majority of Ubuntu users are okay with the stated aims — a bit of anonymous system stat profiling isn’t a major cause for concern, tbh — plus we’re told the metrics will help improve Ubuntu.
Even better: Canonical publishes the results of the survey online for anyone to see.
Ubuntu Report: What Data Does It Collect?
Back to Ubuntu Report.
A check box to opt-out of sending info about your system to Canonical is part of the new first-run tool.
This tool, called “Ubuntu Welcome” greets all Ubuntu users, fresh installs and upgrades alike, the first time they login to Ubuntu 18.04 LTS:
This “Help Improve Ubuntu” page reads:
“Ubuntu can report information that helps improve it. This includes things like the computer model, what software is installed, and the approximate location you choose.”
By default the box to opt-in is selected (“Yes, send system info to Canonical”) but you can easily opt-out (“No, don’t send system info”) should you wish to carry on computing in private.
Placing the “opt out” toggle in the Ubuntu Welcome app is the right idea.
Firstly, I’m generally impatient when I install Ubuntu. I speed-run through whatever screens are put before me in the vain hope of reaching “now installing” screen as soon as humanely possible. If the toggle had opt-out had been in Ubiquity (as initially planned) i’d have missed it.
Secondly, not everyone who uses Ubuntu installs Ubuntu. You can buy laptops pre-loaded with Ubuntu, pre-prepared devices are loaned to siblings, and so on.
Allowing the user and not the installer to decide whether system data is sent out into the digital ether is to be commended.
Here’s My System Data Report
You can see the data collected by Ubuntu Report in your cache folder
It’s important to stress that, no user-identifiable data is collected or sent to Canonical. No account user names, no Ubuntu Single Sign-on details, no IP addresses, nothing.
The report collected on my system queried the following areas:
- Ubuntu version
- OEM/Manufacturer
- Device model number
- BIOS info
- CPU details
- GPU details
- Installed RAM
- Partition Info
- Display(s) details
- Auto-login status
- Live Patching status
- Desktop environment
- Display server
- Timezone
Again; no user name, no IP address, no locale, no list of software or drivers I enabled. Just the same sort of system information I willing show off in screenshots showing the system info tool Neofetch.
Keeping the remit tight means no-one can attribute a system report to any person in particular.
With personal data outside the scope of the tool there’s precious little reason why you wouldn’t want to take part.
After all, by learning more about the hardware and systems we all Ubuntu developers can, in theory, prioritise fixes, support and development accordingly.
Ubuntu learning from its user base.
Will you take part in this Ubuntu system diagnostic reporting? Do you have concerns over the data being collected? Let us (and other readers) know in the comments below.
Home » Feature » This is the Data Ubuntu Collects About Your PC
Since Ubuntu version 16.04, the spyware search facility is now disabled by default. It appears that the campaign of pressure launched by this article has been partly successful. Nonetheless, offering the spyware search facility as an option is still a problem, as explained below. Ubuntu should make the network search a command users can execute from time to time, not a semipermanent option for users to enable (and probably forget).
Even though the factual situation described in the rest of this page has partly changed, the page is still important. This example should teach our community not to do such things again, but in order for that to happen, we must continue to talk about it.
One of the major advantages of free software is that the community protects users from malicious software. Now Ubuntu GNU/Linux has become a counterexample. What should we do?
Proprietary software is associated with malicious treatment of the user: surveillance code, digital handcuffs (DRM or Digital Restrictions Management) to restrict users, and back doors that can do nasty things under remote control. Programs that do any of these things are malware and should be treated as such. Widely used examples include Windows, the iThings, and the Amazon “Kindle” product for virtual book burning, which do all three; Macintosh and the Playstation III which impose DRM; most portable phones, which do spying and have back doors; Adobe Flash Player, which does spying and enforces DRM; and plenty of apps for iThings and Android, which are guilty of one or more of these nasty practices.
Free software gives users a chance to protect themselves from malicious software behaviors. Even better, usually the community protects everyone, and most users don’t have to move a muscle. Here’s how.
Once in a while, users who know programming find that a free program has malicious code. Generally the next thing they do is release a corrected version of the program; with the four freedoms that define free software (see ), they are free to do this. This is called a “fork” of the program. Soon the community switches to the corrected fork, and the malicious version is rejected. The prospect of ignominious rejection is not very tempting; thus, most of the time, even those who are not stopped by their consciences and social pressure refrain from putting malfeatures in free software.
But not always. Ubuntu, a widely used and influential GNU/Linux distribution, has installed surveillance code. When the user searches her own local files for a string using the Ubuntu desktop, Ubuntu sends that string to one of Canonical’s servers. (Canonical is the company that develops Ubuntu.)
This is just like the first surveillance practice I learned about in Windows. My late friend Fravia told me that when he searched for a string in the files of his Windows system, it sent a packet to some server, which was detected by his firewall. Given that first example I paid attention and learned about the propensity of “reputable” proprietary software to be malware. Perhaps it is no coincidence that Ubuntu sends the same information.
Ubuntu uses the information about searches to show the user ads to buy various things from Amazon. Amazon commits many wrongs; by promoting Amazon, Canonical contributes to them. However, the ads are not the core of the problem. The main issue is the spying. Canonical says it does not tell Amazon who searched for what. However, it is just as bad for Canonical to collect your personal information as it would have been for Amazon to collect it. Ubuntu surveillance is not anonymous.
People will certainly make a modified version of Ubuntu without this surveillance. In fact, several GNU/Linux distros are modified versions of Ubuntu. When those update to the latest Ubuntu as a base, I expect they will remove this. Canonical surely expects that too.
Most free software developers would abandon such a plan given the prospect of a mass switch to someone else’s corrected version. But Canonical has not abandoned the Ubuntu spyware. Perhaps Canonical figures that the name “Ubuntu” has so much momentum and influence that it can avoid the usual consequences and get away with surveillance.
Canonical says this feature searches the Internet in other ways. Depending on the details, that might or might not make the problem bigger, but not smaller.
Ubuntu allows users to switch the surveillance off. Clearly Canonical thinks that many Ubuntu users will leave this setting in the default state (on). And many may do so, because it doesn’t occur to them to try to do anything about it. Thus, the existence of that switch does not make the surveillance feature ok.
Even if it were disabled by default, the feature would still be dangerous: “opt in, once and for all” for a risky practice, where the risk varies depending on details, invites carelessness. To protect users’ privacy, systems should make prudence easy: when a local search program has a network search feature, it should be up to the user to choose network search explicitly each time. This is easy: all it takes is to have separate buttons for network searches and local searches, as earlier versions of Ubuntu did. A network search feature should also inform the user clearly and concretely about who will get what personal information of hers, if and when she uses the feature.
If a sufficient part of our community’s opinion leaders view this issue in personal terms only, if they switch the surveillance off for themselves and continue to promote Ubuntu, Canonical might get away with it. That would be a great loss to the free software community.
We who present free software as a defense against malware do not say it is a perfect defense. No perfect defense is known. We don’t say the community will deter malware without fail. Thus, strictly speaking, the Ubuntu spyware example doesn’t mean we have to eat our words.
But there’s more at stake here than whether some of us have to eat some words. What’s at stake is whether our community can effectively use the argument based on proprietary spyware. If we can only say, “free software won’t spy on you, unless it’s Ubuntu,” that’s much less powerful than saying, “free software won’t spy on you.”
It behooves us to give Canonical whatever rebuff is needed to make it stop this. Any excuse Canonical offers is inadequate; even if it used all the money it gets from Amazon to develop free software, that can hardly overcome what free software will lose if it ceases to offer an effective way to avoid abuse of the users.
If you ever recommend or redistribute GNU/Linux, please remove Ubuntu from the distros you recommend or redistribute. If its practice of installing and recommending nonfree software didn’t convince you to stop, let this convince you. In your install fests, in your Software Freedom Day events, in your FLISOL events, don’t install or recommend Ubuntu. Instead, tell people that Ubuntu is shunned for spying.
While you’re at it, you can also tell them that Ubuntu contains nonfree programs and suggests other nonfree programs. (See ) That will counteract the other form of negative influence that Ubuntu exerts in the free software community: legitimizing nonfree software.
The presence of nonfree software in Ubuntu is a separate ethical issue. For Ubuntu to be ethical, that too must be fixed.
This privacy notice tells you about the information we collect from you when you submit your information to us via an enquiry or contact us form on our website. In collecting this information, we are acting as a data controller and, by law, we are required to provide you with information about us, about why and how we use your data, and about the rights you have over your data. For more information, please see our privacy policy.
Who are we?
We are Canonical Group Limited. Our address is 5th Floor Blue Fin Building, 110 Southwark Street, London, SE1 0SU. You can contact us by post at the above address or by email to [email protected] for the attention of “Legal”.
We are not required to have a data protection officer, so any enquiries about our use of your personal data should be addressed to the contact details above.
What personal data do we collect?
When you submit your information to us via an enquiry or contact us form we ask you for your name, your email address, your phone number and related information, including asking questions relating to the nature of your enquiry and permitting free text responses.
Why do we collect this information?
We will use your information to respond to your enquiry This may involve us calling you with a response where we have your phone number in order to do so.
We ask for your consent to do this, and we will only contact you in relation to your enquiry for so long as we have your consent to do so.
If relevant, and where you have agreed, we may also use your information to send you other news and product updates from Canonical. This may involve us calling you, where we have your phone number in order to do so.
We ask for your consent to do this, and we will only send you or tell you about news and product updates for as long as you continue to consent.
What do we do with your information?
Your information is stored in our database and is not shared with any third parties, except as reasonably required for Canonical to process and store your data. It is sent outside of the European Economic Area for our own internal processing purposes only.
How long do we keep your information for?
Your information is kept for as long as you continue to consent to receive our newsletter and for so long as reasonably required thereafter in accordance with our record retention policy.
Your rights over your information
By law, you can ask us what information we hold about you, and you can ask us to correct it if it is inaccurate.
You can also ask for it to be erased and you can ask for us to give you a copy of the information.
You can also ask us to stop using your information for newsletters, news or product updates – the simplest way to do this is to withdraw your consent, which you can do at any time, either by clicking the unsubscribe link at the end of any newsletter or email, or by emailing, writing or telephoning us using the contact details above.
Your right to complain
If you have a complaint about our use of your information, you can contact the Information Commissioner’s Office via their website at or write to them at:
Want a fully managed private cloud?
Canonical provides a managed services option for OpenStack. Our experts take responsibility for the design, deployment and operations.
Get Ubuntu
The open source software platform that runs everywhere from the smartphone, the tablet and the PC to the server and the cloud.
Further reading
- Loading.
© 2021 Canonical Ltd. Ubuntu and Canonical are registered trademarks of Canonical Ltd.
Whenever Ubuntu boots up, a dialogue pops up asking me to unlock my default keyring.
Is there some way this can unlock automatically through PAM or some other magical way?
12 Answers 12
Be warned that this will make your keyring accessible without a password. Period. You don’t have to be logged in to view it
With that being said,
I think the simplest way is to set the password for the keyring to an empty password — you will not be prompted for a password then:
- Open Applications -> Accessories -> Password and Encryption Keys
- Right-click on the “login” keyring
- Select “Change password”
- Enter your old password and leave the new password blank
- Press ok, read the security warning, think about it and if you still want to get rid of this dialog, choose “use unsafe storage”.
Again, as the message says: This will expose all your passwords (e.g. email passwords) that you chose to save in the default keyring to anyone using your computer or having access to your files and is therefore not recommended.
Addendum for Ubuntu 11.04:
In the default Unity session, you can start the application by clicking on the Ubuntu logo in the top left corner, then typing Password, and selecting Password and Encryption Keys from the search result.
In the classic session the path to start the application has changed to System → Preferences → Password and Encryption Keys
Addendum for Ubuntu 11.10:
In the default Unity session, you can start the application by clicking on the Ubuntu launcher (the first item) in the Unity launcher bar on the left side, then typing Password, and selecting Password and Encryption Keys from the search result.
In the classic session (from the gnome-session-fallback package) the path to start the application has again changed to Applications → Other → Password and Encryption Keys
The Read-error on Swap-device error occurs when your Ubuntu system is low on swap memory. Here’s how you can fix the issue.
The Linux operating system is one of the most stable and secure desktop and server operating systems, no wonder that it is the go-to operating system for most servers.
System administrators and engineers love Linux for its stability and performance, but occasionally Linux too experiences performance hiccups.
The “read-error on swap-device” is a relatively common failure on Linux that can cause your system to crash or be non-responsive rendering it unusable. This guide will show you how to fix the read-error on swap-device failure on Ubuntu Linux.
Why Use a Swap File?
A swap file can be a physical storage medium such as a USB drive, a file on a hard drive, or a dedicated partition on a storage medium.
Swap files play an important role because they act as a supplementary medium to the physical RAM on your PC. When you are running memory-intensive processes and your RAM runs out of storage, Linux will use the swap file to run the other applications or store variable data.
Starting with Ubuntu Linux 18.04, the swap area is by default a swap file, prior to that the swap area used to be a dedicated swap partition.
Common Causes of the Read-Error on Swap-Device Failure
Some of the most common causes of failures on swap devices or files include the following:
- Very low RAM on your PC: When you have very low memory left on your system, then most applications will forcibly store variable data in a swap file. Unfortunately reading data from a swap file is much slower than reading from RAM.
- Low swap device storage: Problems will occur if you have a very small swap file with a lot of data stored as variable data, which in turn will lead to low performance of the system.
Looking at the causes mentioned above, we can say that increasing the size of RAM or the swap file can help in fixing the read-error on swap-device issue in Ubuntu.
Viewing Swap File Size
To fix the read-error on the swap device failure, you have to make sure that you have enough storage space on your swap file. Ideally, the size of your swap file should slightly match the size of your RAM.
Run the following command to check the size of your swap file on Ubuntu Linux. In addition, it also lists the RAM space.
As you can see from the output above, this particular PC has a swap file storage of 2GB.
Alternatively, you can also the GUI interface to check the swap file and memory in use. Press the Super + A keyboard keys and search for System Monitor. The graph in the middle shows your memory and swap file usage.
Knowledge of swap file and RAM usage is important for making informed decisions while managing your RAM on Linux.
Creating a Swap File
Before you create or increase the size of your swap file, make sure that you disable the /swapfile using the command below.
Once the swap file has been disabled, you are ready to create a new swap file. For example, to create a swap file of 4G, run the following command.
For security purposes, you should assign your swap file with only read-write permissions on the root user, using the command below.
You can specify that the /swapfile is a swap area using the mkswap utility as below.
Finally, you can enable or start your swap file by running the following command.
Monitoring Your Memory Usage on Linux
Now that you have a swap file with sufficient memory in place, your Linux system will use it accordingly. You can monitor the swap file and RAM usage using the tools defined in this guide. Another option for checking swap file and RAM usage is to use the free -m command.
Low system memory is the primary reason why programs become unresponsive on a computer. Knowing how to kill such programs can be a lifesaver in such situations.
When a Linux app becomes unresponsive and crashes, how can you kill it? Try one of these tricks to kill a stuck program in Linux.
Mwiza develops software by profession and writes extensively on Linux and front-end programming. Some of his interests include history, economics, politics & enterprise-architecture.
Subscribe to our newsletter
Join our newsletter for tech tips, reviews, free ebooks, and exclusive deals!
Is it possible to disable X at boot time? I’m setting up a server so it would be nice if it wouldn’t load the graphical interface every time I boot.
17 Answers 17
Edit /etc/default/grub with your favourite editor, e.g. nano :
For systems that use systemd
This is an additional step for systemd releases, e.g. Ubuntu 15.04, the steps above for grub are still necessary.
You need to tell systemd to not load the graphical login manager:
You will still be able to use X by typing startx after you logged in.
Installing the GUI will probably cause it to start automatically, but it’s very easy to boot to text mode in Ubuntu. Just open /etc/default/grub as root and add text to the
Your system will then always boot to text mode.
If you want to boot to the GUI, just press e in the boot menu and remove text from the kernel line.
If you want to start the GUI after boot, just run:
Hope this helps 🙂
If you want to boot into text mode:
Edit /etc/default/grub . For example:
Then update Grub:
Note: Removing quiet splash (i.e. GRUB_CMDLINE_LINUX_DEFAULT="" ) will show text during boot but then show a graphical login screen as usual. Replacing quiet splash with text will leave you at a login prompt; to start a GNOME session, use sudo /etc/init.d/gdm start or startx .
To disable GDM:
Install bum .
After installation it will be found under System>>Administration>>Bootup-Manager
Uncheck Gnome Display Manager
If you are using lightdm as a login manager it can be prevented from loading by disabling it.
You can use an override:
And to start lightdm on command:
To restore your system so that lightdm is always started on boot:
For more information, the upstart cookbook is your friend:
It has already beed answered in several old questions, but cannot find them just now, so I sum up the various situations here.
To stop an X server started by startx , simply terminate the session.
To stop an X server started by the Login Manager (GDM), run
then move to a tty, for example pressing Ctrl – Alt – F1 , then login here in text mode.
To avoid at all the starting of the Login Manager (and X), modify
changing the line
then update the grub configuration file with
so that the next time you go directly to text mode, and you need startx to initiate a X session, or alternatively sudo service gdm start .
I did following
Step 1 First update your repository by running
sudo apt-get update
Step 2 There is some bug in old version of lightdm, so we need to upgrade the same. To do so run,
sudo apt-get install lightdm
Step 3 Now we have to modify grub config. Step 3a Open /etc/default/grub with your favourite editor and change
Step 3b Also comment GRUB_HIDDEN_TIMEOUT=0 This line is for un-hiding the GRUB menu
Step 4 Now we will upgrade GRUB configuration
Step 5 Ubuntu 11.10 Desktop edition use lightdm for GUI. We need to disable the same
sudo update-rc.d -f lightdm remove
Step 6 Now restart your machine.
Yes, telling the system to start in console at boot time is possible through editing grub command. When you reach grub menu, highlight Ubuntu’s entry and press e .
You will see text such as in the image bellow:
Change the text quiet splash to text . Press F10 to launch. (Source: rolling-ubuntu). I have tested this on my system, 14.04, booted into text console, no lightdm in sight. Started lightdm with sudo initctl start lightdm
To avoid doing so every time, you can add permanent grub entry with such option as suggested in this answer
An alternative suggestion, is to change default runlevel and change runlevels at which lightdm starts/stops, as suggested by another answer on the same post
I noticed this thread revolves around assuming you are using LightDM as the Display Manager. Though this may be the usual DM/welcomer, that isn’t part of the original question. (And he did not specify..)
I use KDE/KDM on my server. Instead, I simply disable the upstart/service from starting under runlevel 2:
/etc/init/kdm.conf: (kdm: 4:4.8.5-0ubuntu0.3 , Upstart Version: 1.5-0ubuntu7.2)
Assuming your default runlevel is 2 on fresh reboot, you will have a console and not KDM. Then you can run DM/DE manually when needed = Use ‘startx’ /etc. To return machine to console and exit X server completely after this, just use ‘log out’.
Other dm .confs scripts are similar. (I setup my server like this.. to be able to work using a GUI occasionally – but, not pull resources when not using/needed or simply rebooting.)
EDIT
(My current system: Upstart 1.12.1 / Ubuntu 14.04)
Due to upstart the way to resolve this lately is to simply disable your Display Manager from starting on boot:
echo “manual” | sudo tee -a /etc/init/ .override
This can be any service in /etc/init including kdm/gdm. ‘startx’ to run as needed following a reboot.
1. Don’t be complacent because you’re running Linux!
It’s easy to have a false sense of security, thinking that other operating system might be more targeted than Linux, but there are plenty of risks and vulnerabilities for all types of Linux devices. Keep your guard up regardless of your OS.
2. Ensure you use a password to protect your user account.
This should be required, but even so, make sure you always use a strong, lengthy password.
3. Don’t use an admin account for daily activity.
For everyday computing, log in with a basic or standard user account. This is likely to be the default behavior when creating a new account, but it’s worth double-checking your account’s status. Note that some system-wide actions will require you to log in with the administrator account because of restricted permissions.
4. Encrypt your data.
Full disk encryption is ideal, but it’s also possible to encrypt just your home directory, for example on a shared machine. This is usually done during installation, and is difficult to do afterwards. In that situation, the easiest solution is to backup your data (always a good thing!) and then re-install the OS selecting encryption options. If you really want to try encrypting an existing system, the process varies depending on your distribution and disk partition setup so it’s best to search for instructions relevant for your environment.
5. Activate your screensaver when idle with screen lock.
Reduce the time for the lock to take effect once the screensaver starts.
6. Review your installed applications.
It’s good practice to keep installed applications to a minimum. Not only does this keep your machine lean, it also reduces your exposure to vulnerabilities. As well as looking through your application list manually, there may be tools available for your distribution to make it easy, such as BleachBit.
7. Keep your system updated.
It’s usually easy to keep both Linux and installed applications up to date. At the very least make sure updates for security are installed automatically.
8. Periodically check for rootkits.
This can be done by installing a rootkit detector such as chkrootkit, which is easily run with the command sudo chkrootkit .
9. Lock down remote connection settings.
If you use SSH for remote access, there are some simple steps to reduce the risk of attack. The easiest is to use a port other than the default port 22 (and below 1024). You can also prevent remotely logging in as root with PermitRootLogin no in the SSH config file. This article has more tweaks for securing SSH.
10. Turn off listening services you don’t need.
Some daemons listen on external ports. Turn these services off if not needed, for example sendmail or bind. This could also improve boot times. To check for listening services, use this command: netstat -lt
11. Make sure you have a firewall running.
Your OS may have a built-in firewall already, probably iptables. Firewalls can be confusing to configure with the command line, but there’s likely to be a GUI frontend available for easier control such as Gufw.
12. Restrict privileged access with SELinux or AppArmor.
These may be installed in your system by default but if not, it’s worth adding and configuring them. They both enable users to define rules that limit how applications can run or affect other processes and files. The benefit is that in the event of an attack, the damage to your system is limited. You can read more here about how to use SELinux and AppArmor.
13. Install DuckDuckGo Privacy Essentials in your browser.
Our Privacy Essentials browser extension has built-in tracker network blocking, smarter encryption, and, of course, private search, all designed to operate seamlessly together while you search and browse the web.
How: Get the extension for popular browsers from
Congratulations! You’ve just taken a big step to increasing privacy and protecting the data on your Linux system.
Credit: Thanks to WarnerJan Veldhuis for SSH port advice.
For more privacy advice follow us on Twitter, and stay protected and informed with our privacy newsletters.
Dax the duck
We're the Internet privacy company for everyone who's had enough of hidden online tracking and wants to take back their privacy now.
Stay protected and informed with our privacy newsletters.
Your email address will not be shared or associated with anonymous searches.
Device Privacy Tips
How to Encrypt Your Devices
How to encrypt your Mac, Windows PC, iPhone and Android, to keep your data and privacy safe.
How to Protect Privacy on Windows 7
Easy steps to protect your data on Microsoft Windows 7. Use these steps to improve privacy and security.
Running Ubuntu directly from either a USB stick or a DVD is a quick and easy way to experience how Ubuntu works for you, and how it works with your hardware. Most importantly, it doesn’t alter your computer’s configuration in any way, and a simple restart without the USB stick or DVD is all that’s needed to restore your machine to its previous state.
With a live Ubuntu, you can do almost anything you can from an installed Ubuntu:
- Safely browse the internet without storing any history or cookie data
- Access files and edit files stored on your computer or USB stick
- Create new office suite documents and save them remotely
- Fix broken configurations to get a computer running again
Requirements
All you need is either a USB stick or DVD with Ubuntu pre-installed. For instructions on how to create these, take a look at one of the following tutorials:
- Create a bootable USB stick on Windows, Ubuntu or macOS
- Burn a DVD on Windows, Ubuntu or macOS
2. Boot from DVD
It’s easy to boot Ubuntu from a DVD. Here’s what you need to do:
- Put the Ubuntu DVD into your optical/DVD drive.
- Restart your computer.
A few moments later you’ll see the language selection menu followed by Ubuntu’s boot options. Select the top entry, Try Ubuntu without installing, and press return.
If you don’t get this menu, take a look at the community DVD guide for help.
3. Boot from USB flash drive
Most computers will boot from USB automatically:
- Insert the USB flash drive
- Restart your computer
You should see the same language selection menu and boot options we saw in the previous ‘Boot from DVD’ step. Select the top entry, Try Ubuntu without installing, and press return.
If your computer doesn’t automatically boot from USB, try holding F12 when your computer first starts. With most machines, this will allow you to select the USB device from a system-specific boot menu.
F12 is the most common key for bringing up your system’s boot menu, but both Escape and F2 are typical alternatives. If you’re unsure, look for a brief message when your system starts – this will often inform you of which key to press to bring up the boot menu.
4. Choose your preferred language
After the desktop has loaded, you’ll see the welcome window. From here, you can select your language from a list on the left and choose between either installing Ubuntu directly, or trying the desktop first. Select Try Ubuntu to launch into the full desktop experience.
5. Enjoy Ubuntu
Your live desktop will appear. Have a look around, check out the new features, and enjoy the simplicity of Ubuntu’s intuitive interface.
You can still choose to install Ubuntu after passing the Welcome pane by clicking on the Install Ubuntu icon on the desktop background.