How to understand the defcon scale
Keyword Analysis
| Keyword | CPC | PCC | Volume | Score | Length of keyword |
|---|---|---|---|---|---|
| military defcon scale | 0.5 | 1 | 4452 | 12 | 21 |
| military | 0.55 | 1 | 3616 | 64 | 8 |
| defcon | 0.62 | 0.1 | 8529 | 72 | 6 |
| scale | 1.29 | 0.2 | 1556 | 49 | 5 |
Keyword Research: People who searched military defcon scale also searched
| Keyword | CPC | PCC | Volume | Score |
|---|---|---|---|---|
| military defcon scale | 1.24 | 0.7 | 9713 | 93 |
Search Results related to military defcon scale on Search Engine
wikihow.com
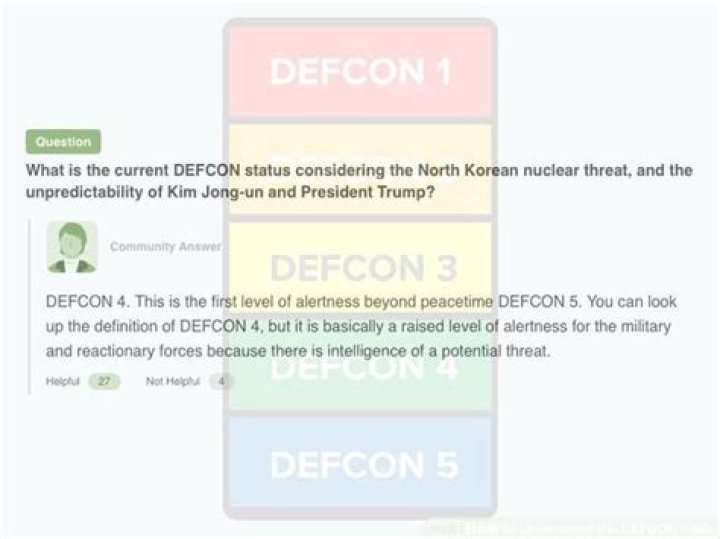
The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely).
DA: 56 PA: 30 MOZ Rank: 70
wikipedia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
DA: 62 PA: 5 MOZ Rank: 44
kipkis.com
The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely).
DA: 23 PA: 92 MOZ Rank: 21
defconlevel.com
The Defcon Levels range from alert status 1 to alert status 5. Defcon level 1 is the highest US military alert status such as a current state of war, or heightened nuclear threat and Defcon level 5 is the systems lowest threat condition such as a current state of peace.
DA: 21 PA: 27 MOZ Rank: 18
wikia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces. The DEFCON system was developed by the Joint Chiefs of Staff and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military, and increase in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match varying .
DA: 49 PA: 63 MOZ Rank: 89
fas.org
During the Cuban Missile Crisis, the US Strategic Air Command was placed on DEFCON 2 for the first time in history, while the rest of US military commands (with the exception of the US Air Forces in Europe) went on DEFCON 3. On 22 October 1962 SAC responded by establishing Defense Condition Three (DEFCON III), and ordered B-52s on airborne alert.
DA: 27 PA: 36 MOZ Rank: 43
defconwarningsystem.com
The Chinese military is planning to conduct a large-scale landing drill off Hainan Island in the South China Sea in August to simulate the possible seizure of the Taiwanese-held Pratas Island in the future, Chinese sources familiar with the matter have said.
DA: 35 PA: 54 MOZ Rank: 58
globalsecurity.org
DEFCON IV DOUBLE TAKE is a situation where military precaution is required owing to smallscale tension. This has been the actual status of the Korean Peninsula since the armistice in 1953.
DA: 29 PA: 39 MOZ Rank: 56
airspacemag.com
In the last case, the military knew that a worldwide hike to DEFCON 3 was not well suited as a response to terrorists using hijacked airliners, but according to Bruce Blair of Princeton University, in the first uncertain hours, authorities seized on it as the quickest way to secure the perimeters of U.S. military bases.
DA: 36 PA: 65 MOZ Rank: 89
Keyword Analysis
| Keyword | CPC | PCC | Volume | Score | Length of keyword |
|---|---|---|---|---|---|
| defcon scale | 1.49 | 0.2 | 1056 | 34 | 12 |
| defcon | 0.63 | 0.8 | 5675 | 89 | 6 |
| scale | 0.52 | 0.6 | 5822 | 75 | 5 |
Keyword Research: People who searched defcon scale also searched
| Keyword | CPC | PCC | Volume | Score |
|---|---|---|---|---|
| define defcon scale | 0.12 | 0.5 | 7032 | 63 |
| military defcon scale | 0.97 | 0.5 | 1860 | 2 |
| the defcon scale | 1.13 | 1 | 855 | 9 |
| defcon scale | 0.03 | 0.3 | 8324 | 36 |
| defcon scale today | 1.54 | 0.7 | 2734 | 67 |
Search Results related to defcon scale on Search Engine
wikipedia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
DA: 4 PA: 85 MOZ Rank: 75
wikihow.com
The United States’ DEFCON (short for “defense readiness condition”) scale is a measure of the level of alertness of the nation’s defense forces. The DEFCON scale uses a minimum of 5 (for normal peacetime status) and a maximum of 1 (for.
DA: 87 PA: 55 MOZ Rank: 76
kipkis.com
The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely). .
DA: 72 PA: 49 MOZ Rank: 51
quora.com
DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
DA: 28 PA: 58 MOZ Rank: 13
fas.org
DEFCON 3 Increase in force readiness above normal readiness DEFCON 2 Further Increase in force readiness, but less than maximum readiness DEFCON 1 Maximum force readiness. EMERGCONs are national level reactions in response to ICBM (missiles in the air) attack. By definition, other forces go to DEFCON 1 during an EMERGCON.
DA: 28 PA: 78 MOZ Rank: 25
djynet.net
The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match varying military situations.
DA: 88 PA: 40 MOZ Rank: 100
defconlevel.com
The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
DA: 76 PA: 52 MOZ Rank: 50
defconlevel.com
The Defcon levels do not reflect internal threats such as that of civil war within the country, riots or other threats happening from within. The Defcon Levels range from alert status 1 to alert status 5. Defcon level 1 is the highest US military alert status such as a current state of war, or heightened nuclear threat and Defcon level 5 is the .
DA: 14 PA: 68 MOZ Rank: 69
defconwarningsystem.com
The DEFCON Warning System is a private intelligence organization which has monitored and assessed nuclear threats by national entities since 1984. It is not affiliated with any government agency and does not represent the alert status of any military branch.
DA: 35 PA: 28 MOZ Rank: 75
defcon.org
defcon.org media.defcon.org defcongroups.org. Future Dates. DEF CON 29 Aug. 5-8, 2021 Book a Room! DEF CON 30 Aug. 11-14, 2022. Speaker’s Corner. DEF CON CFP: Thinking Back and Moving Forward by Nikita. Bridging the Gap: Dispersing Knowledge through Research Presented at DEFCON by Aditya K Sood, PhD. Hackers and Healthcare: A Call To Arms
DA: 53 PA: 94 MOZ Rank: 32
Keyword Analysis
| Keyword | CPC | PCC | Volume | Score | Length of keyword |
|---|---|---|---|---|---|
| defcon scale | 1.11 | 0.7 | 8197 | 43 | 12 |
| defcon | 0.69 | 0.5 | 6520 | 57 | 6 |
| scale | 1.2 | 1 | 7461 | 40 | 5 |
Keyword Research: People who searched defcon scale also searched
| Keyword | CPC | PCC | Volume | Score |
|---|---|---|---|---|
| define defcon scale | 1.69 | 0.4 | 621 | 64 |
| military defcon scale | 1.64 | 0.6 | 6451 | 75 |
| the defcon scale | 1.53 | 0.8 | 4051 | 47 |
| defcon scale | 1.17 | 0.1 | 6231 | 54 |
| defcon scale today | 1.18 | 1 | 3774 | 77 |
Search Results related to defcon scale on Search Engine
wikipedia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
DA: 36 PA: 69 MOZ Rank: 67
wikihow.com
The United States’ DEFCON (short for “defense readiness condition”) scale is a measure of the level of alertness of the nation’s defense forces. The DEFCON scale uses a minimum of 5 (for normal peacetime status) and a maximum of 1 (for.
DA: 71 PA: 26 MOZ Rank: 47
kipkis.com
The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely). .
DA: 90 PA: 1 MOZ Rank: 97
quora.com
DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
DA: 20 PA: 49 MOZ Rank: 86
fas.org
DEFCON 3 Increase in force readiness above normal readiness DEFCON 2 Further Increase in force readiness, but less than maximum readiness DEFCON 1 Maximum force readiness. EMERGCONs are national level reactions in response to ICBM (missiles in the air) attack. By definition, other forces go to DEFCON 1 during an EMERGCON.
DA: 21 PA: 52 MOZ Rank: 7
djynet.net
The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match varying military situations.
DA: 51 PA: 21 MOZ Rank: 73
defconlevel.com
The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
DA: 100 PA: 47 MOZ Rank: 42
defconlevel.com
The Defcon levels do not reflect internal threats such as that of civil war within the country, riots or other threats happening from within. The Defcon Levels range from alert status 1 to alert status 5. Defcon level 1 is the highest US military alert status such as a current state of war, or heightened nuclear threat and Defcon level 5 is the .
DA: 25 PA: 74 MOZ Rank: 99
defconwarningsystem.com
The DEFCON Warning System is a private intelligence organization which has monitored and assessed nuclear threats by national entities since 1984. It is not affiliated with any government agency and does not represent the alert status of any military branch.
DA: 68 PA: 57 MOZ Rank: 67
defcon.org
defcon.org media.defcon.org defcongroups.org. Future Dates. DEF CON 29 Aug. 5-8, 2021 Book a Room! DEF CON 30 Aug. 11-14, 2022. Speaker’s Corner. DEF CON CFP: Thinking Back and Moving Forward by Nikita. Bridging the Gap: Dispersing Knowledge through Research Presented at DEFCON by Aditya K Sood, PhD. Hackers and Healthcare: A Call To Arms
DA: 63 PA: 74 MOZ Rank: 94
Want more to discover? Make Yahoo Your Home Page. See breaking news & more every time you open your browser.
- Home
- News
- Finance
- Fantasy
- Sports
- Shopping
- Weather
- Lifestyle
- All
- Images
- Videos
- News
- Local
- Answers
- Shopping
- Anytime
- Past day
- Past week
- Past month
Get beautiful photos on every new browser tab.
Def-Con 4 – Wikipedia
Def-Con 4 is a 1985 Canadian post-apocalyptic film, portraying three astronauts who survive World War III aboard a space station and return to Earth to find greatly changed circumstances.
- Produced by: Michael Donovan, Paul Donovan, Maura O’Connell
- Music by: Christopher Young
- Release date: March 15, 1985
- Starring: Lenore Zann, Maury Chaykin, Kate Lynch, Kevin King, John Walsch, Tim Choate
DEFCON – Wikipedia
The initial DEFCON system had “Alpha” and “Bravo” conditions (under DEFCON 3) and Charlie/Delta under DEFCON 4, plus an “Emergency” level higher than DEFCON 1 with two conditions: “Defense Emergency” and the highest, “Air Defense Emergency” (“Hot Box” and “Big Noise” for exercises).
DEFCON-4 (1985) – IMDb
Mar 15, 1985 · Directed by Paul Donovan, Digby Cook, Tony Randel. With Lenore Zann, Maury Chaykin, Kate Lynch, Kevin King. Two men and a woman circle the globe in a satellite armed with a nuclear device.
- 4.5/10 (1.8K)
- Director: Paul Donovan, Digby Cook, Tony Randel
- Content Rating: R
DefCon 4 (1985) (film review). : SFcrowsnest
Jun 10, 2019 · For those who don’t know, ‘DefCon 4’ is, apart from the name of this film and the name for a reaction in the event of a world-war nuclear war. Although written as ‘Def-Con 4’, the title in the film has no hyphen, so I shall refer to it as that.
DEF-CON 4 (1985) VHS – YouTube
Defense Condition 4 Howe (Tim Choate), Jordan (Kate Lynch), and Walker (John Walsch) are three U.S. astronauts who return to earth two months after a nuclear holocaust only to confront a stark and.
Amazon.com: Def-Con 4 / Hell Comes to Frogtown (Double .
Def-Con 4: The Last Defense. The Last Hope. Howe (Tim Choate), Jordan (Kate Lynch), and Walker (John Walsch) are three astronauts who return to earth two months after a nuclear holocaust and must confront a new and terrifying reality.
- Format: DVD
Def-Con 4 (1985) – Rotten Tomatoes – Movie Trailers
Jan 06, 2017 · Audience Reviews for Def-Con 4. Feb 14, 2010. Well if you upp some B.horrow Sci fi..this is a movie for you. Martin D Super Reviewer. Jun 15, 2007.
- Category: sci fi
DEFCON Wiki | Fandom
– I’ve made some Wiki-cleanup, and a favicon. – Good news: The extraction of the old pages is done, now comes the import. 2008.01.17 – DEFCON Wiki Logo created – First things first. 🙂 2008.01.14 – DECFON Wiki established – We got the oppurtunity to build a Wiki for the game DEFCON in the Wikia portal. – We started to migrate the content form .
DEF CON – Wikipedia
DEF CON (also written as DEFCON, Defcon or DC) is one of the world’s largest and most notable hacker conventions, held annually in Las Vegas, Nevada.The first DEF CON took place in June 1993 and today many attendees at DEF CON include computer security professionals, journalists, lawyers, federal government employees, security researchers, students, and hackers with a general interest in .
WarGames – Wikipedia
WarGames: Defcon 1, a real-time strategy game that was only loosely related to the film, was released for the PlayStation and PC in 1998. A tile-matching video game , “WarGames: WOPR”, was released for iOS and Android devices in 2012.
Top keyword related from Google/Bing/Yahoo of defcon 1 or 5 worse
Load more
Top URL related to defcon 1 or 5 worse 1. Text link: What do the DEFCON ratings of 1-5 mean? – Quora
Link:
Description: DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
2. Text link: DEFCON – Wikipedia
Link:
Description: The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
3. Text link: How to Understand the DEFCON Scale: 9 Steps (with Pictures)
Link:
Description: Use DEFCON 1 for maximum alertness. DEFCON 1 refers to maximum military readiness — it is thought that forces with a DEFCON level of 1 are kept ready for immediate action at all times. DEFCON 1 is reserved for the absolute most dangerous, severe situations, including imminent or ongoing nuclear war involving the US or one of its allies.
4. Text link: The 5 DEFCON Levels Names Colors And Alert Status Meanings
Link:
Description: The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
5. Text link: Traffic Safety Readiness Level DEFCON 1
Link:
Description: DEFCON 5 is the condition denoting normal readiness, going up to DEFCON 1 which signifies maximum readiness. Similarly, driver training in Europe emphasizes always having a high state of readiness. I passed my driving test in the UK for both motorcycles and cars and have ridden mopeds and motorcycles since I was 16 years old (the UK tests are .
6. Text link: DEFCON: A Documentary About the World’s Largest Hacking .
Link:
Description: One thing that sort of irks me is when people mistake DEFCON 5 as worse and crazier and insane and severe than DEFCON 1. I know more always sounds better but it’s not. That has nothing to do .
7. Text link: Defcon Five – TV Tropes
Link:
Description: The Cheap Trick song Man-U-Lip-U-Lator includes the line “full alert, DEFCON 4.” Even if the scale were 1 to 5 instead of 5 to 1, DEFCON 4 still wouldn’t be full alert. The Dutch Hardstyle company Q-Dance has an open-air festival called Defqon 1, spelled with a Q instead of a C, as it is part of their naming gimmick.
8. Text link: What is Defcon 5,4,3,2,and1? | Yahoo Answers
Link:
Description: in the military wat is Defcon 5,4,3,2,and 1. Answer Save. 6 Answers. Relevance. Lu B. 1 decade ago. Favorite Answer “DEFCON 5 . This is the condition used to designate normal peacetime military readiness. An upgrade in military preparedness is typically made by the Joint Chiefs of Staff and announced by the United States Secretary of Defense.
9. Text link: Has the US ever reached Defcon 1? If so, how and why? – Quora
Link:
Description: In her 2016 book The Pentagon’s Brain: An Uncensored History of DARPA, America’s Top-Secret Military Research Agency, Annie Jacobsen describes such an incident. On October 5, 1960 the newly operating radar station at Thule Air Force Base in Greenl.
Want more to discover? Make Yahoo Your Home Page. See breaking news & more every time you open your browser.
- Home
- Mail
- News
- Finance
- Fantasy
- Sports
- Shopping
- Weather
- Lifestyle
- All
- Videos
- Images
- News
- Local
- Answers
- Shopping
- Anytime
- Past day
- Past week
- Past month
Get beautiful photos on every new browser window.
Used Walrus Audio DEFCON 4 Effect Pedal – Guitar Center
- Big Bang 2020
- – Halloween Essentials
- – Used Effects Pedals
- – Used Amplifiers & Effects
- – Used Effects
- – Used Guitars
- – Shop All Guitars
- – Guitar Center Find Your Sound
- The DEFense readiness CONdition (DEFCON) is an alert state used by the United States Armed Forces. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands.
People also ask
What does Def Con 4 mean?
How to Understand the DEFCON Scale: 9 Steps (with Pictures)
What does DEFCON mean and how does it work?
DEFCON – Wikipedia
What is the DEFCON scale?
Reference
What DEFCON level is the United States in now?
What DEFCON level is the United States in now?
DEFCON-4 (1985) – IMDb
Mar 15, 1985 · “Def Con 4” takes a serious tone, which is occasionally undermined by poor acting and special effects. But the overall impression is quite good. Sure it’s fun to make fun of, but this is largely because we no longer live with the fear of nuclear war on a daily basis.
- 4.5/10 (1.8K)
- Director: Paul Donovan, Digby Cook, Tony Randel
- Content Rating: R
- Video Duration: 2 min
DEFCON – Wikipedia
The initial DEFCON system had “Alpha” and “Bravo” conditions (under DEFCON 3) and Charlie/Delta under DEFCON 4, plus an “Emergency” level higher than DEFCON 1 with two conditions: “Defense Emergency” and the highest, “Air Defense Emergency” (“Hot Box” and “Big Noise” for exercises).
Def-Con 4 – Wikipedia
Def-Con 4 is a 1985 Canadian post-apocalyptic film, portraying three astronauts who survive World War III aboard a space station and return to Earth to find greatly changed circumstances.
- Produced by: Michael Donovan, Paul Donovan, Maura O’Connell
- Music by: Christopher Young
- Release date: March 15, 1985
- Starring: Lenore Zann, Maury Chaykin, Kate Lynch, Kevin King, John Walsch, Tim Choate
Def-Con 4 (1985) – Rotten Tomatoes
Jan 06, 2017 · Audience Reviews for Def-Con 4. Feb 14, 2010. Well if you upp some B.horrow Sci fi..this is a movie for you. Martin D Super Reviewer. Jun 15, 2007.
- Director: Paul Donovan
- Category: sci fi
- Produce Company: New World Video
DEFCON 4 Condition Level – Double Take Or Green Alert Status
DEFCON 4, also called “Double Take” or “Green Alert” is an increase in intel gathering and strengthening of security protocols. DEFCON 4 is considered “Above Normal Readiness”. The alert color for DEFCON 4 is green, also known as Green alert.
What is DEFCON 4 in the DEFCON warning system? – Quora
DEFCON 4 is a condition is ALSO a status where the military tries to convince itself no need to go to DEFCON status one. The launch is seen as an absolute possibility and other branches of the military are used to prevent DEFCON One. so, it can be said DEFCON four is a planning stage that might not have any aircraft “Scrambled” to the skies.
What does DEFCON 1 mean?
What DEFCON level is the United States in now?
What do the DEFCON ratings of 1-5 mean? – Quora
Images for Defcon 4
How to Understand the DEFCON Scale: 9 Steps (with Pictures)
Mar 03, 2020 · DEFCON 4 is the first level of readiness above the baseline value of DEFCON 5 and thus constitutes a fairly mild increase in readiness (though an increase from DEFCON 5 to DEFCON 4 is certainly significant). This DEFCON level signifies increased intelligence-gathering efforts and, sometimes, the heightening of national security measures.
- 92% (71)
- Views: 576.9K
- Video Duration: 3 min
DEFCON DEFense CONdition – United States Nuclear Forces
DEFCON 4 Normal, increased intelligence and strengthened security measures DEFCON 3Increase in force readiness above normal readiness DEFCON 2Further Increase in force readiness, but less than maximum readiness DEFCON 1 Maximum force readiness.
DEFCON on Steam
Inspired by the 1983 cult classic film, Wargames, DEFCON superbly evokes the tension, paranoia and suspicion of the Cold War era, playing on the fascinating aspects of psychological gameplay that occur during strategic nuclear warfare. You play a General hidden deep within an underground bunker.
- 9/10 (2K)
- Developer: Introversion Software
- Price: $9.99
- Genres: Strategy, Wargame, Indie
Economy DEFCON 4 Bunker – DEFCON Bunkers
This is our DEFCON 4 Base single unit underground bunker, bomb shelter, and survival shelter. DEFCON 4 Base units are 8′ x 16′ x 20′ and are 100% steel. DEFCON 4 units come standard with, bullet resistant doors, 45 degree entrance, and many other standard features. They are manufactured by us at our facility in the Midwest USA.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
Recently, we released the exciting new course “Chords and Scales” to add a different dimension to our ever-expanding courses. With this course, you will learn how to accompany many songs with piano chords and even improvise and create your own music using beautifully sounding scales.
So, what are piano Chords and Scales?
Before you venture into the course, it might be helpful to understand some basics.
Western music is based on notes organized in scales. Scales are made of a selection of tones in succession. Each scale delivers a distinct mood and sound. While scales consist of tones played in succession (‘melodically’), chords consist of tones played simultaneously (‘harmonically’).
If this is your first try with chords, you might like this fun introduction with Chrome’s Music Lab!
The C-major Scale
A scale is made up of a sequence of ordered notes, either ascending or descending. Commonly, notes from a single scale are used to compose the melody and chords throughout a song.
Let’s take a look at the most used scale in western music.
The white keys on the piano, starting with C, represent the C-Major Scale.
Any major scale has a particular structure.
You’ll notice this structure if you pay attention to the black keys and the distance between the keys that form the scale.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
C to D is a whole tone step. You’ll recognize a whole tone step by the black key in between the white keys C and D. The same goes for D to E – but notice E to F is a semitone step (with no black key in between). F to G, G to A, and A to B are all whole tone steps, but B to C, again, is a semitone step.
Looking at this, what you’ll find is a certain ‘formula’ made from a specific order of whole tone and semitone steps.
This formula is called The Major Scale . The Major Scale creates a certain melodic feel and mood, which your ears will certainly recognize. The starting note, C, is called the Tonic and it defines the name of the scale.
Let’s take a look at the formula for The Major Scale: (W for whole tone step and S for semitone step):
W W S W W W S
With this formula, you can build The Major Scale all over the keyboard, no matter which key you start with.
Key-Signatures
Try playing a Major Scale starting with G as the tonic, and be sure to follow the exact formula.
G-A-B (semitone) C-D-E-F# (semitone) G.
If you follow the formula, you will sometimes end up with sharps and sometimes with flats – it all depends on where the tonic is! These sets of sharps and flats are what the key signature is made of.
Did you notice you ended up with one black key? This one is called F# (not Gb since you cannot skip a letter when building a scale).
In the case of the G-Major scale, you have one sharp (F#) in the key signature. The sharp at the beginning of the score is valid for every note F in the score.
Check out scales and how they sound like with “Magical Moments I” and ‘Mystical Moments.’
Chords & Arpeggios
Generally speaking, chords are made of three or more tones played simultaneously (harmonically) to create a harmony, and they’re often used to accompany a melody.
When chord tones are played one after the other successively, it’s called an Arpeggio or Broken Chord, and they are also considered Chords.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
The most commonly used piano chords are called Triads, and they’re made up of three notes combined together. You can easily create chords and triads by playing a key and skipping a key.
Let’s go back to the C Major Scale and build a triad. C is the root note – the note the chord is based on. Just skip a note to E, then skip a note to G and you end up with three notes: C, E and G. Those are your triad notes for the C-Major Triad.
Major and Minor Chords
Play the notes of the C-major triad at the same time. Sounds happy and hopeful, right? Remember how it feels when you play a major chord. Subsequently, you can build a triad starting with the root D.
Then you have D, F, and A. Now, play these notes all at the same time. But hey, do you notice the chord sounds different than the Major Chord? It’s much more melancholic and sad, right? That’s because it’s a Minor chord.
Learn more about the reasons why minor and major chords sound different in this article.
You may go on to play a triad starting with all the notes in the scale by building a third, then another third. 7 different chords can be found in a scale because there are 7 different notes.
This is why a song may have many chords but stays in the same key because all the notes in the chords are made up of a single scale.
The recipe for piano chords
Good to remember:
- Major triad: To create a major triad, play any key on your keyboard. Then play the key you find 4 semitone steps up from the root note. Then play the key another 3 semitone steps up.
- To create a minor triad, play any key on your keyboard. Then play the key 3 semitone steps up from the root note. Then play the key another 4 semitone steps up.
- When you see a chord symbol Em, you know that the root note is E, then “m” means minor.
- If a chord symbol is a letter only, like “F”, then it’s always a major chord.
Test your knowledge and jump to our first chord course: “ Meet the Chords I.”
Stay tuned for more “tips and tricks” blog posts like this one. There will be regular posts to help you gain more knowledge and skills to accompany your journey with Skoove.
I hope this blog post was helpful, please feel free to leave us a comment.
Defense readiness conditions (DEFCONs) describe progressive alert postures primarily for use between the Joint Chiefs of Staff and the commanders of unified commands. DEFCONs are graduated to match situations of varying military severity, and are numbered 5,4,3,2, and 1 as appropriate. DEFCONs are phased increases in combat readiness. In general terms, these are descriptions of DEFCONs:
DEFCON 5 Normal peacetime readiness
DEFCON 4 Normal, increased intelligence and strengthened security measures
DEFCON 3 Increase in force readiness above normal readiness
DEFCON 2 Further Increase in force readiness, but less than maximum readiness
DEFCON 1 Maximum force readiness.
EMERGCONs are national level reactions in response to ICBM (missiles in the air) attack. By definition, other forces go to DEFCON 1 during an EMERGCON.
DEFENSE EMERGENCY: Major attack upon U.S. forces overseas, or allied forces in any area, and is confirmed either by the commander of a unified or specified command or higher authority or an overt attack of any type is made upon the United States and is confirmed by the commander of a unified or specified command or higher authority.
AIR DEFENSE EMERGENCY: Air defense emergency is an emergency condition, declared by the Commander in Chief, North American Aerospace Defense Command. It indicates that attack upon the continental United States, Canada, or US installations in Greenland by hostile aircraft or missiles is considered probable, is imminent, or is taking place.
During the Cuban Missile Crisis, the US Strategic Air Command was placed on DEFCON 2 for the first time in history, while the rest of US military commands (with the exception of the US Air Forces in Europe) went on DEFCON 3. On 22 October 1962 SAC responded by establishing Defense Condition Three (DEFCON III), and ordered B-52s on airborne alert. Tension grew and the next day SAC declared DEFCON II, a heightened state of alert, ready to strike targets within the Soviet Union.
On 15 November 1965 the day Strategic Air Command (SAC) postured down to defense condition (DEFCON) III.
On 6 October 1973 Egyptian and Syrian forces launched a surprise attack on Israel. On 25 October U.S. forces went on Defense Condition (DEFCON) III alert status, as possible intervention by the Soviet Union was feared. On 26 October, CINCSAC and CINCONAD reverted to normal DEFCON status. On 31 October USEUCOM (less the Sixth Fleet) went off DEFCON III status. The Sixth Fleet resumed its normal DEFCON status on 17 November 1973.
Sources and Resources
FAS | Nuke | Guide | USA | C3I |||| Index | Search |
Maintained by Webmaster
Updated Wednesday, April 29, 1998 7:46:18 AM
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
This year at Defcon, the car hacking village is bigger than ever, says Cameron Camp. Key observation? The tools are getting better.
This year at Defcon, the car hacking village is bigger than ever, with more cars, car hacking adapters and giant snarls of tiny exposed wires tied to demo stations with car parts screwed to plywood stands than ever before. It’s car hacking 101 here, and class is in full force.
The first thing you notice is the tools are getting better. They’re simpler, easier to buy, and they even have a car hacking badge you can buy that is sort of shaped like a car and has an ODB-II interface on one end (those sold our pretty fast) in case you want to dig in.
And lots of folks do – this place is packed. Last year there was a smattering of workstations and a somewhat smaller snarl of wires – not so this year.
This year the automotive sophistication is increasing, but only a little. Basically most critical messages that your car digests to run its critical systems are in a plain, unencrypted form that are digested by default and then run the part of your car they’re responsible for. Except for a couple of mobile systems like the odometer, much of the rest of the car has the “implicit availability” model baked in, meaning the modules will almost always listen and act, but do very little to determine if the message is legitimate.
But the car folks have at least started to notice the legitimacy issue in a sort of formal way, drafting up some secure car specs they hope will eventually find their way into real cars. For now it’s just a design goal. If you bought a car today, it doesn’t have this. If you already have a car, it really doesn’t have this, or anything close.
“The problem is that security costs money and the car folks are hyper sensitive to increasing production costs.”
The problem is that security costs money and the car folks are hyper sensitive to increasing production costs. On your home router you feel like if it costs less than $50, you don’t care. Car manufacturers would care about $50 per car. A lot. Multiply every dollar spent by a million units and you start to understand.
The good news is that authentication can be handled in software, it’s just that as of yet, it hasn’t been in large-scale production. So this means the costs can (eventually) be low, once the non-recoverable expense of designing and implementing the system has been recovered. Even then, seemingly simple changes or additions to a car are ridiculously expensive to implement. This is because cars, in general, have different design goals than more traditional electronic doodads.
Consider how upset you’d be if your $50 router failed. Hint: Not very. How about if you’re $50,000 full-size SUV failed while carrying your kids to school. Very unhappy. Like lawsuit unhappy. So while car companies have taken heat for not being earlier to the game, there is an implicit expectation for the devices they produce to basically last forever, whereas you’d be happy if your router lasted more than a couple of years.
Still, if you were a cybersecurity expert who knows a lot about the nuts and bolts of cars, you’d basically have guaranteed employment unless you did something grossly inappropriate – and maybe even then. Automotive security isn’t going away. Neither are the prognostications of automotive gloom and doom. But the industry is making progress. We hope next year at Defcon there will be even more folks trying to figure out how to secure the platform and share constructively with the auto industry so we’ll all be safe.
Data: U.S. Bureau of Labor Statistics via St. Louis Fed; Chart: Naema Ahmed/Axios
Sentence from a nightmare: 6.6 million Americans filed for unemployment last week, a decline from the previous week’s 6.9 million.
The big picture: Over the past three weeks, 1 in 10 working-age adults filed for unemployment, Axios’ Courtenay Brown notes.
Why it matters: We’re not even close to understanding the long-term ramifications of America rocketing from sub-4% unemployment to what could be Depression levels in about a month.
- This is just the first wave, since we don’t know how many businesses will fail while waiting on reopening or bailouts.
- Once the lockdowns end, we don’t know how businesses will behave in a world where the next lockdown is just a new outbreak away.
But we do know:
- More pain is on the way, and it will be felt with savage inequity.
- We mustn’t become numb to the scale of these numbers.
- We each must play our role: If you’re not an essential worker, that means staying home and avoiding group gatherings.
The bottom line: Now is the time to behave in ways that you can recount with pride for future generations.
The metric system provides units of measurement for distance, volume, mass, time, and temperature. It builds these units using a basic unit and a set of prefixes.
The following list shows five important basic units in the metric system.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
The following table shows ten metric prefixes, with the three most commonly used in bold.
Prefix Meaning Number Power of Ten Giga- One billion 1,000,000,000 10 9 Mega- One million 1,000,000 10 6 Kilo- One thousand 1,000 10 3 Hecta- One hundred 100 10 2 Deca- Ten 10 10 1 (none) One 1 10 0 Deci- One tenth 0.1 10 -1 Centi- One hundredth 0.01 10 -2 Milli- One thousandth 0.001 10 -3 Micro- One millionth 0.000001 10 -6 Nano- One billionth 0.000000001 10 -9
Large and small metric units are formed by linking a basic unit with a prefix. For example, linking the prefix kilo- to the basic unit meter gives you the kilometer, which means 1,000 meters. Similarly, linking the prefix milli- to the basic unit liter gives you the milliliter, which means 0.001 (one thousandth) of a liter.
Here’s a list giving you the basics:
Units of distance: The basic metric unit of distance is the meter (m). Other common units are millimeters (mm), centimeters (cm), and kilometers (km):
1 kilometer = 1,000 meters
1 meter = 100 centimeters
1 meter = 1,000 millimeters
Units of fluid volume: The basic metric unit of fluid volume (also called capacity) is the liter (L). Another common unit is the milliliter (mL):
1 liter = 1,000 milliliters
Note: One milliliter is equal to 1 cubic centimeter (cc).
Units of mass: Technically speaking, the metric system measures not weight but mass. Weight is the measurement of how strongly gravity pulls an object toward Earth. Mass, however, is the measurement of the amount of matter an object has. If you traveled to the moon, your weight would change, so you would feel lighter. But your mass would remain the same, so all of you would still be there. Unless you’re planning a trip into outer space or performing a scientific experiment, you probably don’t need to know the difference between weight and mass.
The basic unit of weight in the metric system is the gram (g). Even more commonly used, however, is the kilogram (kg):
1 kilogram = 1,000 grams
Note: 1 kilogram of water has a volume of 1 liter.
Units of time: As in the English system, the basic metric unit of time is a second (s). For most purposes, people also use other English units such as minutes, hours, and so forth.
For many scientific purposes, the second is the only unit used to measure time. Large numbers of seconds and small fractions of sections are represented with scientific notation.
Units of speed: For most purposes, the most common metric unit of speed (also called velocity) is kilometers per hour (km/hr). Another common unit is meters per second (m/s).
Units of temperature (degrees Celsius or Centigrade): The basic metric unit of temperature is the Celsius degree (°C), also called the Centigrade degree. The Celsius scale is set up so that at sea level, water freezes at 0°C and boils at 100°C.
Scientists often use another unit — the Kelvin (K) — to talk about temperature. The degrees are the same size as in Celsius, but 0 K is set at absolute zero, the temperature at which atoms don’t move at all. Absolute zero is approximately equal to –273.15°C.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
This story appears in the June 15, 2015 issue of Forbes. Subscribe
I recently attended John Mauldin’s Strategic Investment Conference, an annual event that brings together some of the best minds in finance and economics. With some two dozen speakers in two and a half days, the word “intense” best describes the proceedings. I came away thinking that the world is not on the brink of crisis but that crisis is an ever present concern. Most could see a bright future, if only we could transition smoothly from the significant, self-inflicted problems we have amassed since the 2008 downturn.
Most of the speakers identified the major financial bubbles currently threatening our economy–from junk bonds to housing prices and the U.S. dollar–but offered few solutions. After all, we are in uncharted waters today, and neither the Federal Reserve nor Congress really knows which way to go. Our world has become so interlinked that no one wants to take actions that could start a currency or trade war. We live not in a world of policy action but of policy reaction. The Fed and the European Central Bank have become firemen, not statesmen.
The current state of the world argues for defensive posturing. The consensus is that we will not restore normal economic growth without some trauma. While the timing of the next crisis is uncertain, history tells us that overstaying in the market is more costly than getting out early. But is it too early? Since the timing, depth and origins of any crisis are uncertain, let’s take a chapter out of the U.S. military’s playbook for dealing with threats. They use the term DEFCON, which means Defense Readiness Condition or an alert state. For the purposes of your portfolio, think of DEFCON as Defensive Financial Condition:
DEFCON 1–This is where I judge we are today.
Positioning Fixed Income For What’s To Come
Forbes/SHOOK Raise $1.4 Million, A Record For Make-A-Wish
Avoid Being A Commodity, Branding Expert Tells SHOOKtalks
- Keep a balance of cash of at least 10%.
Invest up to 10% in gold (GLD) and silver (SLV) ETFs. Set trailing stop-loss orders on your holdings with long-term gains. DEFCON 2–Volatility breaks out in the markets driven by a buildup of negative events either here or abroad.
- Increase your cash position to 15%.
- Take all your long-term gains; hold off on taking losses until year-end.
- Set trailing stop-loss orders on all your low-dividend/interest-paying holdings.
- Invest up to 15% in gold (GLD) and silver (SLV) ETFs.
- Buy out-of-the-money puts on ETFs that best mirror your remaining exposed positions.
- Buy some inverse ETFs tied to indexes to offset value declines in your holdings. To short stock indexes I recommend the ProShares lineup; for the Dow 30 use (DOG), for the S&P 500 (SH), for the QQQ (PSQ) and for the Russell 2000 (RWM).
DEFCON 3–A panic has begun somewhere that has spilled over into the securities markets.
- Liquidate all low-and no-income equities.
- Keep ready cash at home as well as gold.
- Be patient. Turn off the financial TV shows. Free advice is worthless. Let events play out because corrections involve several levels of action and reaction.
DEFCON 4–The crisis is well under way, with no end is in sight. Central banks are pursuing conflicting goals.
- Go to the mattresses (for example, cash, gold and silver).
Investors who need steady income should be aware that while bonds, preferred stocks, MLPs and REITs also decline in a crisis, they will normally continue to pay out interest and dividends and will be among the first to recover because of their high payouts. Hence, you may opt to ride out the volatility in an income security.
While I have faith that central bankers have learned much about how to handle the next crisis, their first priority will be to protect the banking system and their bosses, i.e., the government. Not investors. When the crisis hits you will hear lots of happy talk designed to calm rather than inform. One former Fed governor at the conference, Larry Meyer, concluded with these encouraging words: “Good luck–you’ll need it.”
Richard Lehmann is editor of the Forbes/Lehmann Income Securities Investor newsletter and president of Lehmann Fridson Advisors.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
I’m a former Forbes columnist, investment advisor and publisher of the Forbes/Lehmann Distressed Municipal Debt Report. As a lifetime investor in postage stamps, I’ve
The “Vitruvian Man” approach to building knowledge, wisdom, and foresight.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
Hemant Mohapatra on LinkedIn: “I’m taking book recommendations to.
I’m taking book recommendations to get a firmer understanding of the world at large — a sort of 101 on the fundamental…
A few weeks ago I put up a note on my LinkedIn (see above) about books that can form the building blocks to our understanding of just about everything there is to know in this universe. Essentially, I wanted to understand why are we the way we are and why have our social, political and biological systems evolved into what they are today.
The response was so good that it took me over a month to get this post together with the top 50 of the over 100+ recommendations.
I call it my “planet-scale meta-intelligence” book-list. Why planet-? To imply that all knowledge that has ever existed in the history of mankind is compressed into these 50 books. Why meta-? It certainly won’t teach you quantum mechanics or calculus — that’s too specific — but it’ll tell you why those tools were needed, when, and the part they played to get us to where we are today.
The next challenge was how to organize the list. Sure, I could fit them into history, science, psychology & influence, economics, and so on but that felt too formulaic. In thinking about how to build my intellect, I was inspired by the idea of the Vitruvian Man by Leonardo Da Vinci, who believed “the workings of the human body to be an analogy for the workings of the universe.”[ref]. Okay, Cool, Leo, but get some underwear on.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
So I divided the selection into five categories:
Core: similar to working out in the gym, this part is the most important one and also the ideal starting point. Everything builds out of here. These books cover the principles of how this world works at an elemental level. A weak core makes rest of the knowledge unapproachable.
Mind: this covers how to become a better strategist, develop foresight, patience, and smarter intellectual habits. Together with the core, these two form the basics of further development IMHO.
Torso: a better upper body is often the end goal — it’s the most visible, the most outwardly attractive, and appeals to the ego. The books in this category therefore cater to matters of charisma, influence, and power.
Legs: often the most ignored part of the gym routine: leg days! Without this, your reach in the world is always going to be limited. This section covers operational experience, stories of building empires, of failures, and discipline.
Soul: finally, it’s tough to stay the course without an inspiring story or a personal passion that drives you out of bed to hit the gym. Similarly, this section focuses on feeding the soul with stories of struggles and wins against exceptional odds, stories of growth through deeply meaningful failures, and stories of redemption.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
The right distribution of the topics is personal. I prefer to focus a lot more on the fundamentals: core & mind, and then divide the rest. Take it as-is but YMMV. So, without further ado, here is the list, starting with the Core. All link out to Amazon US. Again, the full list is here.
Why it is completely asinine to join as sales rep #1 : DEFCON 1–5
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
Morando Method: Sales Wound #143
The 2nd most common question I get asked on a weekly basis is, “Should I join a startup?”
If you’re hellbent on getting startup experience (aka joining “the $hitshow,”) hopefully it’s because you want to start your own company one day. Otherwise, stay where you are. Here are the dimensions I would use myself to evaluate the level of “$hitshow” : DEFCON 1– 5
As a baseline, let’s assume the team is strong technically and can ship code on a regular basis.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
The founders have never closed an annual contract before in their career. Eject now .
Why? Closing/Shipping Revenue is just like shipping code. It’s binary, you’ve either done it or you haven’t. If you have never worked with a customer to get them to sign a piece of paper that commits them to working with you for 12 months, then I cannot begin explain how hard this is to do. It’s like explaining to your grandma what it takes to push code to Prod.
Closing an Opportunity for $10k/mo on a month2month contract where the customer can leave immediately is a 2/10 on the “difficulty of sale” scale.
Closing an Opportunity for $2k/mo for a committed, “no-outs” 12 month term is a 9/10 on the difficulty scale.
It’s not about the deal size, it’s about the time of commitment. In order to sell an annual contract at any ARR you have to sell deeper into the psychology of the buyer and higher in the org chart.
Founders “say” they understand the value of engaging with customers as an Enterprise partner. You really like their solution and you see the market opportunity.
If that’s the case then let’s experiment.
The first thing I strongly suggest founders do is to go get a contract signed. Size of the contract isn’t important. Length of the contract (12 mo) though is an absolute requirement. Only then, will you understand 20% of what it takes to be a sales pro. But you’ll have learned the single most important thing, CONTEXT.
You can work with the founders to help them qualify leads / pitch prospects / position product / close opportunities but do NOT do it for them. You’re in the background coaching them and you don’t have to be 100% on the team yet.
Typically after a founder closes the first annual contract, unassisted, the lightbulb goes off. They are beginning to learn and understand why sales is just as important as Engineering. Ship Code : Ship Revenue.
Founders have closed an annual contract. The larger the committed ACV = less risky.
But you’ll be the first sales rep hire. Roll the dice.
I’d always bet on the founders + team. If you feel you align well with them in your mindset, motivation and teamwork style then go for it. You’ll know within the first 30 days if you’ve been oversold OR you’ve oversold your skills.
Founders have closed an annual contract: AND
- There is at least 1 AE on the team
Even better as you can assess the level of experimentation the 1st AE has done. This is just an accelerator to figuring out phase 1. It’s not about how much commission the AE is making but whether the AE can close and how much assistance they need from the team. It’s ok if the founder is still on every call in the “Presales Engineer” role but that will give you a sense of how independent the AE can be based on where the product + customer fit is. getting closer to the first mini phase of repeatability.
Founders have closed an annual contract AND
- The founders have enterprise sales experience + exceptional engineering
- Engineering has had 12+ months working with real customer issues
Do whatever it takes to get onboard asap. If that means taking $0 to just get on the team to prove yourself, then do it. In 30 days they’ll be screaming to get you officially on the payroll.
Bonus: if the founders have ever worked with me before, then you’ll know that they are Defcon 5 as the first thing I advocate is the Founder needs to first close deals so they get direct context re: how difficult sales really is. No One knows how hard it is to get someone to sign a contract unless you’ve specifically done it. No One.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
By Holly Hovan MSN, APRN, CWOCN-AP
A series analyzing the use of the Braden Scale for Predicting Pressure Sore Risk® in the long-term care setting. For Part 2, click here.
As wound care professionals, the Braden Scale for Predicting Pressure Sore Risk® is near and dear to our hearts. With that in mind, our evidence-based tool needs to be used correctly in order to yield accurate results. Working with long-term care and geriatric populations opens up a world of multiple pre-existing comorbidities and risk factors that aren’t always explicitly written into the Braden Scale categories. Additionally, the frequency of the Braden Scale may also contribute to a multitude of different scores; the resident behaves differently on different shifts, for example, asleep on night shift but up and about on days. What is the correct way to score them? I believe that a less frequent Braden Scale assessment yields more accurate results. However, we should still complete a Braden Scale on admission, transfer, receiving, and most importantly, with any change in condition.
What is the Braden Scale?
Briefly put, the Braden Scale is an evidenced-based tool, developed by Nancy Braden and Barbara Bergstrom, that predicts the risk for developing a hospital or facility acquired pressure ulcer/injury. The Braden Scale uses a scores from less than or equal to 9 to as high as 23. The lower the number, the higher the risk for developing an acquired ulcer/injury.
19-23 = no risk
15-18 = mild risk
13-14 = moderate risk
less than 9 = severe risk
There are six categories within the Braden Scale: sensory perception, moisture, activity, mobility, nutrition, and friction/shear.
In this blog, I will be addressing sensory perception as defined by the Braden Scale, and how this is applicable to residents of a long-term care facility.
Braden Scale Scoring for Sensory Perception
Sensory perception: the ability to respond meaningfully to pressure-related discomfort.
The resident is scored on a scale of 1-4 in the categories below:
1: Completely limited
2: Very limited
3: Slightly limited
4: No impairment
Please review the Braden Scale card for a deeper definition of each of these terms. With regard to sensory perception, I want to stress the importance of assessing neuropathy in residents with diabetes, recognizing paralysis/loss of sensation with spinal cord injury (SCI) residents, and understanding how sensory perception may vary in the dementia population.
These three populations are often seen in long-term care facilities, so it’s important to understand their unique situations. Most people recognize SCI as a loss of sensory perception, but diabetic neuropathy is sometimes missed. A simple monofilament test may be used to check for sensation/neuropathy in residents with diabetes. In addition, vascular status should be assessed, including pulses on the lower extremities and capillary refill.
After assessing for neuropathy and possibly vascular issues, the definitions of the Braden Scale for each of the subcategories (1-4) should be read and understood, and an appropriate number assigned to the subcategory. A resident with paraplegia experiencing loss of sensation to the lower half of the body would automatically only score a 2 due to loss of sensation over half of the body. A resident with diabetes with some neuropathy in the feet would automatically score a 3 if they cannot feel pain or discomfort in one or more of their extremities.
The subcategory “no impairment” is very rarely accurate with the long-term care population. These residents are in the hospital, scooting up in bed, spending more time in bed, possibly wheelchair bound, have multiple pre-existing comorbidities, and usually one or more deficits. It is possible to score a 4 here, but again, rare.
The take away point here for sensory perception is to assess for neuropathy, SCI, and dementia. These residents may often be deficient in this specific category. It is important to understand the category and definitions in order to accurately score the resident. Education with nursing staff is pertinent here, and pocket cards are always helpful. Yearly competencies for long-term care staff on Braden Scale education are also helpful, along with orientation for new nurses, to be sure that the information is understood. Education by a certified wound, ostomy and continence nurse, continued support, and follow-up are needed to ensure accurate Braden Scale scores within any facility.
Up next: The Braden Scale subcategory MOISTURE.
Note: For anyone who wishes to utilize the Braden Scale in their health care facility, you must request permission to do so. Please visit and complete the Permission Request form.
About the Author
Holly is a board certified gerontological nurse and advanced practice wound, ostomy, and continence nurse coordinator at The Department of Veterans Affairs Medical Center in Cleveland, Ohio. She has a passion for education, teaching, and our veterans. Holly has been practicing in WOC nursing for approximately six years. She has much experience with the long-term care population and chronic wounds as well as pressure injuries, diabetic ulcers, venous and arterial wounds, surgical wounds, radiation dermatitis, and wounds requiring advanced wound therapy for healing. Holly enjoys teaching new nurses about wound care and, most importantly, pressure injury prevention. She enjoys working with each patient to come up with an individualized plan of care based on their needs and overall medical situation. She values the importance of taking an interprofessional approach with wound care and prevention overall, and involves each member of the health care team as much as possible. She also values the significance of the support of leadership within her facility and the overall impact of great teamwork for positive outcomes.
The views and opinions expressed in this blog are solely those of the author, and do not represent the views of WoundSource, Kestrel Health Information, Inc., its affiliates, or subsidiary companies.
To revist this article, visit My Profile, then View saved stories.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
To revist this article, visit My Profile, then View saved stories.
In the middle of the Planet Hollywood Resort & Casino convention hall in Las Vegas, amid workshops on cryptography and digital defense, a hospital will soon be humming with activity—or at least a pretty good facsimile of one. Visitors will wander through a radiology department, a pharmacy, a laboratory, and an intensive care unit. And it’ll be stocked with all the devices you’d find in a real medical center. The difference is that here, they’re supposed to get hacked.
The Medical Device Village, housed within the DefCon hacking conference BioHacking Village and opening Thursday, has previously consisted of a small table with a few medical devices available for hacking. A few FDA reps and manufacturers would talk researchers through their defenses. But as horror stories about vulnerable pacemakers or insulin pumps persist, and ransomware continues to target hospitals around the world, that more casual approach has felt increasingly insufficient. This year, it’s going all out.
“Medicine feels like one of the last industries to adopt technology in a secure, controllable way,” says Nina Alli, executive director of the BioHacking Village and a health care security researcher. “And for a long time medical device manufacturers wouldn’t come to DefCon. But they’ve become more open to working with researchers. They’re realizing that they can just get an email about a vulnerability out of the blue, or they can form relationships.”
Until very recently, most of this activity would have been not just infeasible but illegal. Medical devices only won a Digital Millennium Copyright Act exemption in 2016, allowing researchers to hack the devices without breaking the law.
Alli makes clear that previous versions of the Medical Device Village still led to some important conversations and security findings. But this year will include not just a mock hospital but also a formal capture the flag hacking competition, and much more extensive hands-on hacking. It also stresses the scope and reach of medical devices beyond high-profile implants like pacemakers. Health care environments are stuffed with sensors, scanners, monitors, and PCs that all connect to networks that share massive amounts of sensitive data. Representatives from 10 large medical device makers, including Philips Health, Medtronic, Abbott, and Becton Dickinson, will bring their expertise and insight into proprietary devices. Only a handful showed up last year.
Those companies have also thrown financial support behind the idea. DefCon doesn’t fund the villages it hosts, though it does provide space for free. After spending $5,000 to $10,000 of their own money on the Medical Device Village last year, the organizers established a nonprofit that has raised funds from medical device manufacturers and the research community for this year’s event and beyond.
“We value and support the involvement and unique perspective of independent security researchers, and appreciate their contributions to the security of our products,” says Erika Winkels, a spokesperson for Medtronic, a medical device manufacturer whose products have come under scrutiny from security researchers. “Their work helps make us better.”
This year’s village also builds on the organizers’ prior work like the Hippocratic Oath for Connected Medical Devices and a collaboration with the FDA for the village, announced in January, called We Heart Hackers. The organizers, who also include neurology researcher Sydney Swaine-Simon, independent security researcher Adrian Sanabria, and Beau Woods, a cybersafety innovation fellow at the Atlantic Council, came together in part through the grassroots computer security and human safety initiative I Am The Cavalry.
To fully grapple with the scale of the medical device security challenge, the village will be an immersive hospital setting complete with hospital rooms and a full complement of medical gadgets as you walk through. The environment, and the larger BioHacking Village, will also feature art pieces created by artists who live with or have experiences with medical devices and other biohacking.
Keyword Analysis
Keyword CPC PCC Volume Score Length of keyword defcon levels explained 0.31 0.5 9233 81 23 defcon 1.27 1 1872 4 6 levels 0.38 0.6 4815 50 6 explained 1.04 0.3 9011 86 9
Keyword Research: People who searched defcon levels explained also searched
Keyword CPC PCC Volume Score defcon levels explained 0.45 0.5 5096 55
Search Results related to defcon levels explained on Search Engine
defconlevel.com
The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
DA: 83 PA: 39 MOZ Rank: 1
wikipedia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
DA: 51 PA: 58 MOZ Rank: 18
wikihow.com
Learn how to read the DEFCON scale. The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely).
DA: 100 PA: 65 MOZ Rank: 91
explained.today
DEFCON explained. The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military.
DA: 6 PA: 77 MOZ Rank: 13
defconlevel.com
After NORAD’s creation in 1957 the first DEFCON warning alert system in history was introduced. In the beginning the defense condition system was more complex and had 3 readiness levels: normal, increased and maximum and were divided into 8 alert conditions that were later simplified.
DA: 38 PA: 63 MOZ Rank: 78
quora.com
DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
DA: 12 PA: 43 MOZ Rank: 42
militarymortgagecenter.com
The DEFCON system prescribes graduated levels of readiness and states of alert and increases from levels of least to most severe. As of this moment our current military status is DEFCON 4. Defcon Levels and What They Mean. DEFCON Level 5. The normal level of peacetime readiness, DEFCON 5 serves as the baseline for the military.
DA: 11 PA: 26 MOZ Rank: 50
defconwarningsystem.com
The following are the recommended steps to take for each of the different DEFCON Warning System Alert Levels. The pubic is advised that these are only recommendations and that each individual must determine for themselves what they should do at a particular time. DEFCON 5 – Green. This is the standard peacetime alert level. All is quiet.
DA: 17 PA: 35 MOZ Rank: 65
The guidance below will help you to understand who can apply for funding, the sort of projects the Defence and Security Accelerator (DASA) funds, and the terms and conditions of DASA contracts.Who .
DA: 72 PA: 25 MOZ Rank: 42
An in-depth survey carried out amongst 100 of those attending this year’s DEFCON conference in Las Vegas recently has revealed that an overwhelming 96 percent of the respondents said they believed the cloud would open up more hacking opportunities for them.
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
“While ‘only’ 12 percent said they hacked cloud systems for financial gain, that still means a sizeable headache for any IT manager planning to migrate their IT resources into the cloud” said Barmak Meftah, CPO with Fortify.
According to Meftah, when you factor in the prediction from numerous analysts that at the start of 2010 20 percent of businesses would have their IT resources in the cloud within four years, you begin to appreciate the potential scale and complexity of the security issues involved.
In the many predictions, he explained, 20 per cent of organizations would own no appreciable IT assets, but would instead rely on cloud computing resources – the same resources that 45 percent of the DEFCON attendees in the survey cheerfully admitted to already having tried to hack.
Breaking down the survey responses, 21 percent believe that SaaS cloud systems are viewed as being the most vulnerable, with 33 percent of the hackers having discovered public DNS vulnerabilities, followed by log files (16 per cent) and communication profiles (12 per cent) in their cloud travels.
Remember, says Meftah, we are talking about hackers having discovered these types of vulnerabilities in the cloud, rather than merely making an observation.
Acronym Definition DEFCON Defense Readiness Condition DEFCON Defense Condition DEFCON Defence Contract Condition DEFCON Define Constant (mathematics)
Want to thank TFD for its existence? Tell a friend about us, add a link to this page, or visit the webmaster’s page for free fun content.
Link to this page:
- Facebook
- Twitter
- ▲
- DEESMI
- DEESMT
- DEESTH
- DEESWEB
- DEET
- DEETM
- DEETS
- DEETYA
- DEEU
- DEEVAL
- DEEWR
- DEF
- DEF MAINT
- DEF-STAN
- DEFA
- DEFAC
- DEFACTO
- DEFAISE
- DEFAIT
- DEFAS
- DEFAT
- DEFB
- DEFBTN
- DEFC
- DEFCOM
- DEFCON
- DEFCON 1
- DEFCON 2-4
- DEFCON 5
- DEFCOS
- DEFD
- DEFDARS
- DEFECM
- DEFENDER
- DEFENSIVE
- DEFET
- DEFF
- DEFG
- DEFHR
- DEFI
- DEFIMNET
- DEFINTELSCOL
- DEFIS
- DEFL
- DEFLE
- DefLink
- DEFLOWH
- DEFM
- DEFMIS
- DEFN
- DEFO
- ▼
- ▲
- defaulter
- defaulter
- defaulter
- defaulter
- defaulter
- defaulters
- defaulters
- defaulters
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting on
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults on
- Défauts sous Revêtement
- DEFB
- DEFBTN
- DEFC
- DEFCAP
- DEFCAP-L/S
- DEFCOM
- DEFCON
- DEFCON 1
- DEFCON 2-4
- DEFCON 5
- DEFCOS
- DEFD
- DEFDARS
- Defeasable interest
- Defeasable interest
- defeasance
- defeasance
- defeasance
- Defeasance Clause
- defeasance fee
- Defeasanced
- Defeasanced
- Defeasanced
- defeasances
- defeasances
- defeasances
- defeasibility
- defeasibility
- defeasible
- defeasible
- defeasible fee
- Defeasible reasoning
- Defeasible reasoning
- Defeasible Reasoning and Uncertainty Management Systems
- Defeasible Reasoning and Uncertainty Management Systems II
- defeasiblely
- defeasiblely
- ▼
- Facebook Share
- Twitter
CITE
- Terms of Use
- Privacy policy
- Feedback
- Advertise with Us
Copyright © 2003-2020 Farlex, Inc
All content on this website, including dictionary, thesaurus, literature, geography, and other reference data is for informational purposes only. This information should not be considered complete, up to date, and is not intended to be used in place of a visit, consultation, or advice of a legal, medical, or any other professional.
More Articles
- Instructions for Weight Watchers Scales
- How to Calculate How Much I’m Lifting
- How to Use a Balance Beam Scale
- Difference Between Gazelle Edge & Gazelle Freestyle
- How to Calculate BMI
A digital scales is a much more precise and uniform tool for measuring items than a manual scale. Digital scales also make measuring ingredients for recipes much easier and accurate, especially for those who are on diets and need to monitor their food intake. Digital scales come in numerous styles, however most have similar features and are generally simple to operate. Using a digital scale can seem a little confusing at first, but these steps will explain how to read a digital scale.
Follow the manufacturer’s instructions for turning the digital scale on. The scale should automatically begin with a reading of zero, reflecting that there is no weight on the scale. Set aside two quantities to be weighed for learning purposes. One should be very lightweight, such as 1/4 cup of flour and one should be a heavier weight, such as a head of lettuce.
Instructions for Weight Watchers Scales
Digital scales measure weight in units of measurement such as pounds (lbs), ounces (oz), kilograms (kg) and grams (g). Place a light object on the scale. Look at the number that is displayed on the LCD screen. Next to that number will be a unit of measurement. This gives you the weight for that specific item. For example, 10 kilograms would read 10kg.
Place a heavier item on the scale. Again, take note of the number and unit of measurement displayed on the LCD screen. For example, a head of lettuce that weighs 1 1/2 pounds will read 1.5 lbs. This is a useful tool to know when measuring out amounts for recipes.
How to Calculate How Much I’m Lifting
Digital scales also have a feature that allows you to weigh an item while it is in a container. This feature is called the tare feature. The tare feature is often used for liquids and items that cannot easily be placed directly on the scale. Use the tare feature by placing a container on the scale. Press the button that says “Tare.” This will reset the scale back to zero and will not record the weight of the container. Place the item you would like to measure into the container. The digital scale will display the weight of the item in the container not including the container itself. The tare feature will display weight on the LCD screen in the same manner as standard measurements.
Try weighing a variety of items to get used to reading the LCD display. Refer to the units of measurement in Step 2 if you are unsure of their abbreviations on the LCD. Turn the scale off when you are finished weighing.
Follow manufacturer’s instructions for advanced features.
Zscaler™ ThreatLabZ contributed to the Verizon 2019 Data Breach Investigations Report
![How to Understand the DEFCON Scale How to Understand the DEFCON Scale]()
As a society, we are more connected than ever before. Our community is no longer just the people living nearby. It is now a global community, made up of disparate individuals connected not by proximity but by the internet.
As in almost any community, crime is a factor. In today’s digital society, that means cybercriminals, and they seem to be launching new attacks every day.
These cybercriminals have gone from lone hackers to sophisticated criminal organizations, launching attacks on individuals, corporations, and governments. As these criminals have become more organized, the challenge in fighting them has become more difficult. If the cybercriminals are working together to increase their chances of success, it makes sense that those who fight these bad actors should also work together.
Today, Verizon released its 2019 Data Breach Investigations Report, and I am proud that the Zscaler ThreatLabZ team once again actively contributed to the findings in this report.
The Verizon 2019 Data Breach Investigations Report takes an in-depth look at security incidents and data breaches that occurred in 2018. The report analyzes 41,686 security incidents, of which 2,013 were confirmed data breaches. It looks at how the results have or have not changed over the years and digs into the overall threat landscape and the actors, actions, and assets that are present in breaches.
The report delves into security incident patterns and describes how they correlate to the various industry verticals. In addition to these primary patterns, the report includes a subset of data to pull out financially motivated social engineering (FMSE) attacks, which are more focused on credential theft and duping people into transferring money into adversary-controlled accounts.
Among the findings, the report revealed that 43 percent of data breaches occurred at small businesses, which tend to have less stringent security than larger organizations, making them an easier target. The most common tactic used in breaches was hacking (52 percent of the time), while errors (21 percent) and misuse by authorized users (15 percent) also led to breaches. And, as can be expected, financial gain was the most common motivation (71 percent).
These results, and the others detailed in the report, are based on data collected from a variety of sources, including publicly disclosed security incidents, cases provided by the Verizon Threat Research Advisory Center (VTRAC) investigators, and external collaborators, such as ThreatLabZ. The year-to-year data includes new sources of incident and breach data as more organizations share information to improve the diversity and coverage of real-world events.
The number of organizations providing data continues to grow, with 66 organizations external to Verizon now contributing to this report. This community of data contributors represents an international group of public and private entities that understand the importance of sharing information to gain a better understanding of the threats we all face on a daily basis.
This is the second consecutive year that Zscaler has provided transaction data for the report. The ThreatLabZ team examined transactions processed in the Zscaler cloud during 2018, specifically looking for attempted phishing attacks and blocked malware. We also offered insights into each threat category with supporting telemetry information indicating the number of users affected by these security incidents and data breaches.
It is heartening to see so many organizations coming together to share information in an ongoing effort to secure the internet and this digital world in which we all participate. Unfortunately, cybercriminals will continue developing new threats and attack methods, as long as there’s a potential payoff. And, since there is no sign of attackers stopping any time soon, it is up to all of us working in the cloud and cybersecurity industries to work together to make their job a lot more difficult.
I think Gloria Macapagal Arroyo, the 14 th President of the Philippines, said it very well: “The power of one, if fearless and focused, is formidable, but the power of many working together is better.”
Deepen Desai is vice president of security research at Zscaler
1. Text link: What do the DEFCON ratings of 1-5 mean? – Quora
Link:
Description: DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
2. Text link: DEFCON – Wikipedia
Link:
Description: The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
3. Text link: How to Understand the DEFCON Scale: 9 Steps (with Pictures)
Link:
Description: Use DEFCON 1 for maximum alertness. DEFCON 1 refers to maximum military readiness — it is thought that forces with a DEFCON level of 1 are kept ready for immediate action at all times. DEFCON 1 is reserved for the absolute most dangerous, severe situations, including imminent or ongoing nuclear war involving the US or one of its allies.
4. Text link: The 5 DEFCON Levels Names Colors And Alert Status Meanings
Link:
Description: The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
5. Text link: Traffic Safety Readiness Level DEFCON 1
Link:
Description: DEFCON 5 is the condition denoting normal readiness, going up to DEFCON 1 which signifies maximum readiness. Similarly, driver training in Europe emphasizes always having a high state of readiness. I passed my driving test in the UK for both motorcycles and cars and have ridden mopeds and motorcycles since I was 16 years old (the UK tests are .
6. Text link: DEFCON: A Documentary About the World’s Largest Hacking .
Link:
Description: One thing that sort of irks me is when people mistake DEFCON 5 as worse and crazier and insane and severe than DEFCON 1. I know more always sounds better but it’s not. That has nothing to do .
7. Text link: Defcon Five – TV Tropes
Link:
Description: The Cheap Trick song Man-U-Lip-U-Lator includes the line “full alert, DEFCON 4.” Even if the scale were 1 to 5 instead of 5 to 1, DEFCON 4 still wouldn’t be full alert. The Dutch Hardstyle company Q-Dance has an open-air festival called Defqon 1, spelled with a Q instead of a C, as it is part of their naming gimmick.
8. Text link: What is Defcon 5,4,3,2,and1? | Yahoo Answers
Link:
Description: in the military wat is Defcon 5,4,3,2,and 1. Answer Save. 6 Answers. Relevance. Lu B. 1 decade ago. Favorite Answer “DEFCON 5 . This is the condition used to designate normal peacetime military readiness. An upgrade in military preparedness is typically made by the Joint Chiefs of Staff and announced by the United States Secretary of Defense.
9. Text link: Has the US ever reached Defcon 1? If so, how and why? – Quora
Link:
Description: In her 2016 book The Pentagon’s Brain: An Uncensored History of DARPA, America’s Top-Secret Military Research Agency, Annie Jacobsen describes such an incident. On October 5, 1960 the newly operating radar station at Thule Air Force Base in Greenl.
Want more to discover? Make Yahoo Your Home Page. See breaking news & more every time you open your browser.
- Home
- News
- Finance
- Fantasy
- Sports
- Shopping
- Weather
- Lifestyle
- All
- Videos
- Images
- News
- Local
- Answers
- Shopping
- Anytime
- Past day
- Past week
- Past month
Get beautiful photos on every new browser window.
Used Walrus Audio DEFCON 4 Effect Pedal – Guitar Center
- Big Bang 2020
- – Halloween Essentials
- – Used Effects Pedals
- – Used Amplifiers & Effects
- – Used Effects
- – Used Guitars
- – Shop All Guitars
- – Guitar Center Find Your Sound
- The DEFense readiness CONdition (DEFCON) is an alert state used by the United States Armed Forces. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands.
People also ask
What does Def Con 4 mean?
How to Understand the DEFCON Scale: 9 Steps (with Pictures)
What does DEFCON mean and how does it work?
DEFCON – Wikipedia
What is the DEFCON scale?
Reference
What DEFCON level is the United States in now?
What DEFCON level is the United States in now?
DEFCON-4 (1985) – IMDb
Mar 15, 1985 · “Def Con 4” takes a serious tone, which is occasionally undermined by poor acting and special effects. But the overall impression is quite good. Sure it’s fun to make fun of, but this is largely because we no longer live with the fear of nuclear war on a daily basis.
- 4.5/10 (1.8K)
- Director: Paul Donovan, Digby Cook, Tony Randel
- Content Rating: R
- Video Duration: 2 min
DEFCON – Wikipedia
The initial DEFCON system had “Alpha” and “Bravo” conditions (under DEFCON 3) and Charlie/Delta under DEFCON 4, plus an “Emergency” level higher than DEFCON 1 with two conditions: “Defense Emergency” and the highest, “Air Defense Emergency” (“Hot Box” and “Big Noise” for exercises).
Def-Con 4 – Wikipedia
Def-Con 4 is a 1985 Canadian post-apocalyptic film, portraying three astronauts who survive World War III aboard a space station and return to Earth to find greatly changed circumstances.
- Produced by: Michael Donovan, Paul Donovan, Maura O’Connell
- Music by: Christopher Young
- Release date: March 15, 1985
- Starring: Lenore Zann, Maury Chaykin, Kate Lynch, Kevin King, John Walsch, Tim Choate
Def-Con 4 (1985) – Rotten Tomatoes
Jan 06, 2017 · Audience Reviews for Def-Con 4. Feb 14, 2010. Well if you upp some B.horrow Sci fi..this is a movie for you. Martin D Super Reviewer. Jun 15, 2007.
- Director: Paul Donovan
- Category: sci fi
- Produce Company: New World Video
DEFCON 4 Condition Level – Double Take Or Green Alert Status
DEFCON 4, also called “Double Take” or “Green Alert” is an increase in intel gathering and strengthening of security protocols. DEFCON 4 is considered “Above Normal Readiness”. The alert color for DEFCON 4 is green, also known as Green alert.
What is DEFCON 4 in the DEFCON warning system? – Quora
DEFCON 4 is a condition is ALSO a status where the military tries to convince itself no need to go to DEFCON status one. The launch is seen as an absolute possibility and other branches of the military are used to prevent DEFCON One. so, it can be said DEFCON four is a planning stage that might not have any aircraft “Scrambled” to the skies.
What does DEFCON 1 mean?
What DEFCON level is the United States in now?
What do the DEFCON ratings of 1-5 mean? – Quora
Images for Defcon 4
How to Understand the DEFCON Scale: 9 Steps (with Pictures)
Mar 03, 2020 · DEFCON 4 is the first level of readiness above the baseline value of DEFCON 5 and thus constitutes a fairly mild increase in readiness (though an increase from DEFCON 5 to DEFCON 4 is certainly significant). This DEFCON level signifies increased intelligence-gathering efforts and, sometimes, the heightening of national security measures.
- 92% (71)
- Views: 576.9K
- Video Duration: 3 min
DEFCON DEFense CONdition – United States Nuclear Forces
DEFCON 4 Normal, increased intelligence and strengthened security measures DEFCON 3Increase in force readiness above normal readiness DEFCON 2Further Increase in force readiness, but less than maximum readiness DEFCON 1 Maximum force readiness.
DEFCON on Steam
Inspired by the 1983 cult classic film, Wargames, DEFCON superbly evokes the tension, paranoia and suspicion of the Cold War era, playing on the fascinating aspects of psychological gameplay that occur during strategic nuclear warfare. You play a General hidden deep within an underground bunker.
- 9/10 (2K)
- Developer: Introversion Software
- Price: $9.99
- Genres: Strategy, Wargame, Indie
Economy DEFCON 4 Bunker – DEFCON Bunkers
This is our DEFCON 4 Base single unit underground bunker, bomb shelter, and survival shelter. DEFCON 4 Base units are 8′ x 16′ x 20′ and are 100% steel. DEFCON 4 units come standard with, bullet resistant doors, 45 degree entrance, and many other standard features. They are manufactured by us at our facility in the Midwest USA.
Recently, we released the exciting new course “Chords and Scales” to add a different dimension to our ever-expanding courses. With this course, you will learn how to accompany many songs with piano chords and even improvise and create your own music using beautifully sounding scales.
So, what are piano Chords and Scales?
Before you venture into the course, it might be helpful to understand some basics.
Western music is based on notes organized in scales. Scales are made of a selection of tones in succession. Each scale delivers a distinct mood and sound. While scales consist of tones played in succession (‘melodically’), chords consist of tones played simultaneously (‘harmonically’).
If this is your first try with chords, you might like this fun introduction with Chrome’s Music Lab!
The C-major Scale
A scale is made up of a sequence of ordered notes, either ascending or descending. Commonly, notes from a single scale are used to compose the melody and chords throughout a song.
Let’s take a look at the most used scale in western music.
The white keys on the piano, starting with C, represent the C-Major Scale.
Any major scale has a particular structure.
You’ll notice this structure if you pay attention to the black keys and the distance between the keys that form the scale.
C to D is a whole tone step. You’ll recognize a whole tone step by the black key in between the white keys C and D. The same goes for D to E – but notice E to F is a semitone step (with no black key in between). F to G, G to A, and A to B are all whole tone steps, but B to C, again, is a semitone step.
Looking at this, what you’ll find is a certain ‘formula’ made from a specific order of whole tone and semitone steps.
This formula is called The Major Scale . The Major Scale creates a certain melodic feel and mood, which your ears will certainly recognize. The starting note, C, is called the Tonic and it defines the name of the scale.
Let’s take a look at the formula for The Major Scale: (W for whole tone step and S for semitone step):
W W S W W W S
With this formula, you can build The Major Scale all over the keyboard, no matter which key you start with.
Key-Signatures
Try playing a Major Scale starting with G as the tonic, and be sure to follow the exact formula.
G-A-B (semitone) C-D-E-F# (semitone) G.
If you follow the formula, you will sometimes end up with sharps and sometimes with flats – it all depends on where the tonic is! These sets of sharps and flats are what the key signature is made of.
Did you notice you ended up with one black key? This one is called F# (not Gb since you cannot skip a letter when building a scale).
In the case of the G-Major scale, you have one sharp (F#) in the key signature. The sharp at the beginning of the score is valid for every note F in the score.
Check out scales and how they sound like with “Magical Moments I” and ‘Mystical Moments.’
Chords & Arpeggios
Generally speaking, chords are made of three or more tones played simultaneously (harmonically) to create a harmony, and they’re often used to accompany a melody.
When chord tones are played one after the other successively, it’s called an Arpeggio or Broken Chord, and they are also considered Chords.
The most commonly used piano chords are called Triads, and they’re made up of three notes combined together. You can easily create chords and triads by playing a key and skipping a key.
Let’s go back to the C Major Scale and build a triad. C is the root note – the note the chord is based on. Just skip a note to E, then skip a note to G and you end up with three notes: C, E and G. Those are your triad notes for the C-Major Triad.
Major and Minor Chords
Play the notes of the C-major triad at the same time. Sounds happy and hopeful, right? Remember how it feels when you play a major chord. Subsequently, you can build a triad starting with the root D.
Then you have D, F, and A. Now, play these notes all at the same time. But hey, do you notice the chord sounds different than the Major Chord? It’s much more melancholic and sad, right? That’s because it’s a Minor chord.
Learn more about the reasons why minor and major chords sound different in this article.
You may go on to play a triad starting with all the notes in the scale by building a third, then another third. 7 different chords can be found in a scale because there are 7 different notes.
This is why a song may have many chords but stays in the same key because all the notes in the chords are made up of a single scale.
The recipe for piano chords
Good to remember:
- Major triad: To create a major triad, play any key on your keyboard. Then play the key you find 4 semitone steps up from the root note. Then play the key another 3 semitone steps up.
- To create a minor triad, play any key on your keyboard. Then play the key 3 semitone steps up from the root note. Then play the key another 4 semitone steps up.
- When you see a chord symbol Em, you know that the root note is E, then “m” means minor.
- If a chord symbol is a letter only, like “F”, then it’s always a major chord.
Test your knowledge and jump to our first chord course: “ Meet the Chords I.”
Stay tuned for more “tips and tricks” blog posts like this one. There will be regular posts to help you gain more knowledge and skills to accompany your journey with Skoove.
I hope this blog post was helpful, please feel free to leave us a comment.
Defense readiness conditions (DEFCONs) describe progressive alert postures primarily for use between the Joint Chiefs of Staff and the commanders of unified commands. DEFCONs are graduated to match situations of varying military severity, and are numbered 5,4,3,2, and 1 as appropriate. DEFCONs are phased increases in combat readiness. In general terms, these are descriptions of DEFCONs:
- DEFCON 5 Normal peacetime readiness
DEFCON 4 Normal, increased intelligence and strengthened security measures
DEFCON 3 Increase in force readiness above normal readiness
DEFCON 2 Further Increase in force readiness, but less than maximum readiness
DEFCON 1 Maximum force readiness.
EMERGCONs are national level reactions in response to ICBM (missiles in the air) attack. By definition, other forces go to DEFCON 1 during an EMERGCON.
- DEFENSE EMERGENCY: Major attack upon U.S. forces overseas, or allied forces in any area, and is confirmed either by the commander of a unified or specified command or higher authority or an overt attack of any type is made upon the United States and is confirmed by the commander of a unified or specified command or higher authority.
AIR DEFENSE EMERGENCY: Air defense emergency is an emergency condition, declared by the Commander in Chief, North American Aerospace Defense Command. It indicates that attack upon the continental United States, Canada, or US installations in Greenland by hostile aircraft or missiles is considered probable, is imminent, or is taking place.
During the Cuban Missile Crisis, the US Strategic Air Command was placed on DEFCON 2 for the first time in history, while the rest of US military commands (with the exception of the US Air Forces in Europe) went on DEFCON 3. On 22 October 1962 SAC responded by establishing Defense Condition Three (DEFCON III), and ordered B-52s on airborne alert. Tension grew and the next day SAC declared DEFCON II, a heightened state of alert, ready to strike targets within the Soviet Union.
On 15 November 1965 the day Strategic Air Command (SAC) postured down to defense condition (DEFCON) III.
On 6 October 1973 Egyptian and Syrian forces launched a surprise attack on Israel. On 25 October U.S. forces went on Defense Condition (DEFCON) III alert status, as possible intervention by the Soviet Union was feared. On 26 October, CINCSAC and CINCONAD reverted to normal DEFCON status. On 31 October USEUCOM (less the Sixth Fleet) went off DEFCON III status. The Sixth Fleet resumed its normal DEFCON status on 17 November 1973.
Sources and Resources
FAS | Nuke | Guide | USA | C3I |||| Index | Search |
Maintained by Webmaster
Updated Wednesday, April 29, 1998 7:46:18 AM
This year at Defcon, the car hacking village is bigger than ever, says Cameron Camp. Key observation? The tools are getting better.
This year at Defcon, the car hacking village is bigger than ever, with more cars, car hacking adapters and giant snarls of tiny exposed wires tied to demo stations with car parts screwed to plywood stands than ever before. It’s car hacking 101 here, and class is in full force.
The first thing you notice is the tools are getting better. They’re simpler, easier to buy, and they even have a car hacking badge you can buy that is sort of shaped like a car and has an ODB-II interface on one end (those sold our pretty fast) in case you want to dig in.
And lots of folks do – this place is packed. Last year there was a smattering of workstations and a somewhat smaller snarl of wires – not so this year.
This year the automotive sophistication is increasing, but only a little. Basically most critical messages that your car digests to run its critical systems are in a plain, unencrypted form that are digested by default and then run the part of your car they’re responsible for. Except for a couple of mobile systems like the odometer, much of the rest of the car has the “implicit availability” model baked in, meaning the modules will almost always listen and act, but do very little to determine if the message is legitimate.
But the car folks have at least started to notice the legitimacy issue in a sort of formal way, drafting up some secure car specs they hope will eventually find their way into real cars. For now it’s just a design goal. If you bought a car today, it doesn’t have this. If you already have a car, it really doesn’t have this, or anything close.
“The problem is that security costs money and the car folks are hyper sensitive to increasing production costs.”
The problem is that security costs money and the car folks are hyper sensitive to increasing production costs. On your home router you feel like if it costs less than $50, you don’t care. Car manufacturers would care about $50 per car. A lot. Multiply every dollar spent by a million units and you start to understand.
The good news is that authentication can be handled in software, it’s just that as of yet, it hasn’t been in large-scale production. So this means the costs can (eventually) be low, once the non-recoverable expense of designing and implementing the system has been recovered. Even then, seemingly simple changes or additions to a car are ridiculously expensive to implement. This is because cars, in general, have different design goals than more traditional electronic doodads.
Consider how upset you’d be if your $50 router failed. Hint: Not very. How about if you’re $50,000 full-size SUV failed while carrying your kids to school. Very unhappy. Like lawsuit unhappy. So while car companies have taken heat for not being earlier to the game, there is an implicit expectation for the devices they produce to basically last forever, whereas you’d be happy if your router lasted more than a couple of years.
Still, if you were a cybersecurity expert who knows a lot about the nuts and bolts of cars, you’d basically have guaranteed employment unless you did something grossly inappropriate – and maybe even then. Automotive security isn’t going away. Neither are the prognostications of automotive gloom and doom. But the industry is making progress. We hope next year at Defcon there will be even more folks trying to figure out how to secure the platform and share constructively with the auto industry so we’ll all be safe.
Data: U.S. Bureau of Labor Statistics via St. Louis Fed; Chart: Naema Ahmed/Axios
Sentence from a nightmare: 6.6 million Americans filed for unemployment last week, a decline from the previous week’s 6.9 million.
The big picture: Over the past three weeks, 1 in 10 working-age adults filed for unemployment, Axios’ Courtenay Brown notes.
Why it matters: We’re not even close to understanding the long-term ramifications of America rocketing from sub-4% unemployment to what could be Depression levels in about a month.
- This is just the first wave, since we don’t know how many businesses will fail while waiting on reopening or bailouts.
- Once the lockdowns end, we don’t know how businesses will behave in a world where the next lockdown is just a new outbreak away.
But we do know:
- More pain is on the way, and it will be felt with savage inequity.
- We mustn’t become numb to the scale of these numbers.
- We each must play our role: If you’re not an essential worker, that means staying home and avoiding group gatherings.
The bottom line: Now is the time to behave in ways that you can recount with pride for future generations.
The metric system provides units of measurement for distance, volume, mass, time, and temperature. It builds these units using a basic unit and a set of prefixes.
The following list shows five important basic units in the metric system.
The following table shows ten metric prefixes, with the three most commonly used in bold.
| Prefix | Meaning | Number | Power of Ten |
|---|---|---|---|
| Giga- | One billion | 1,000,000,000 | 10 9 |
| Mega- | One million | 1,000,000 | 10 6 |
| Kilo- | One thousand | 1,000 | 10 3 |
| Hecta- | One hundred | 100 | 10 2 |
| Deca- | Ten | 10 | 10 1 |
| (none) | One | 1 | 10 0 |
| Deci- | One tenth | 0.1 | 10 -1 |
| Centi- | One hundredth | 0.01 | 10 -2 |
| Milli- | One thousandth | 0.001 | 10 -3 |
| Micro- | One millionth | 0.000001 | 10 -6 |
| Nano- | One billionth | 0.000000001 | 10 -9 |
Large and small metric units are formed by linking a basic unit with a prefix. For example, linking the prefix kilo- to the basic unit meter gives you the kilometer, which means 1,000 meters. Similarly, linking the prefix milli- to the basic unit liter gives you the milliliter, which means 0.001 (one thousandth) of a liter.
Here’s a list giving you the basics:
Units of distance: The basic metric unit of distance is the meter (m). Other common units are millimeters (mm), centimeters (cm), and kilometers (km):
1 kilometer = 1,000 meters
1 meter = 100 centimeters
1 meter = 1,000 millimeters
Units of fluid volume: The basic metric unit of fluid volume (also called capacity) is the liter (L). Another common unit is the milliliter (mL):
1 liter = 1,000 milliliters
Note: One milliliter is equal to 1 cubic centimeter (cc).
Units of mass: Technically speaking, the metric system measures not weight but mass. Weight is the measurement of how strongly gravity pulls an object toward Earth. Mass, however, is the measurement of the amount of matter an object has. If you traveled to the moon, your weight would change, so you would feel lighter. But your mass would remain the same, so all of you would still be there. Unless you’re planning a trip into outer space or performing a scientific experiment, you probably don’t need to know the difference between weight and mass.
The basic unit of weight in the metric system is the gram (g). Even more commonly used, however, is the kilogram (kg):
1 kilogram = 1,000 grams
Note: 1 kilogram of water has a volume of 1 liter.
Units of time: As in the English system, the basic metric unit of time is a second (s). For most purposes, people also use other English units such as minutes, hours, and so forth.
For many scientific purposes, the second is the only unit used to measure time. Large numbers of seconds and small fractions of sections are represented with scientific notation.
Units of speed: For most purposes, the most common metric unit of speed (also called velocity) is kilometers per hour (km/hr). Another common unit is meters per second (m/s).
Units of temperature (degrees Celsius or Centigrade): The basic metric unit of temperature is the Celsius degree (°C), also called the Centigrade degree. The Celsius scale is set up so that at sea level, water freezes at 0°C and boils at 100°C.
Scientists often use another unit — the Kelvin (K) — to talk about temperature. The degrees are the same size as in Celsius, but 0 K is set at absolute zero, the temperature at which atoms don’t move at all. Absolute zero is approximately equal to –273.15°C.
This story appears in the June 15, 2015 issue of Forbes. Subscribe
I recently attended John Mauldin’s Strategic Investment Conference, an annual event that brings together some of the best minds in finance and economics. With some two dozen speakers in two and a half days, the word “intense” best describes the proceedings. I came away thinking that the world is not on the brink of crisis but that crisis is an ever present concern. Most could see a bright future, if only we could transition smoothly from the significant, self-inflicted problems we have amassed since the 2008 downturn.
Most of the speakers identified the major financial bubbles currently threatening our economy–from junk bonds to housing prices and the U.S. dollar–but offered few solutions. After all, we are in uncharted waters today, and neither the Federal Reserve nor Congress really knows which way to go. Our world has become so interlinked that no one wants to take actions that could start a currency or trade war. We live not in a world of policy action but of policy reaction. The Fed and the European Central Bank have become firemen, not statesmen.
The current state of the world argues for defensive posturing. The consensus is that we will not restore normal economic growth without some trauma. While the timing of the next crisis is uncertain, history tells us that overstaying in the market is more costly than getting out early. But is it too early? Since the timing, depth and origins of any crisis are uncertain, let’s take a chapter out of the U.S. military’s playbook for dealing with threats. They use the term DEFCON, which means Defense Readiness Condition or an alert state. For the purposes of your portfolio, think of DEFCON as Defensive Financial Condition:
DEFCON 1–This is where I judge we are today.
Positioning Fixed Income For What’s To Come
Forbes/SHOOK Raise $1.4 Million, A Record For Make-A-Wish
Avoid Being A Commodity, Branding Expert Tells SHOOKtalks
- Keep a balance of cash of at least 10%.
DEFCON 2–Volatility breaks out in the markets driven by a buildup of negative events either here or abroad.
- Increase your cash position to 15%.
- Take all your long-term gains; hold off on taking losses until year-end.
- Set trailing stop-loss orders on all your low-dividend/interest-paying holdings.
- Invest up to 15% in gold (GLD) and silver (SLV) ETFs.
- Buy out-of-the-money puts on ETFs that best mirror your remaining exposed positions.
- Buy some inverse ETFs tied to indexes to offset value declines in your holdings. To short stock indexes I recommend the ProShares lineup; for the Dow 30 use (DOG), for the S&P 500 (SH), for the QQQ (PSQ) and for the Russell 2000 (RWM).
DEFCON 3–A panic has begun somewhere that has spilled over into the securities markets.
- Liquidate all low-and no-income equities.
- Keep ready cash at home as well as gold.
- Be patient. Turn off the financial TV shows. Free advice is worthless. Let events play out because corrections involve several levels of action and reaction.
DEFCON 4–The crisis is well under way, with no end is in sight. Central banks are pursuing conflicting goals.
- Go to the mattresses (for example, cash, gold and silver).
Investors who need steady income should be aware that while bonds, preferred stocks, MLPs and REITs also decline in a crisis, they will normally continue to pay out interest and dividends and will be among the first to recover because of their high payouts. Hence, you may opt to ride out the volatility in an income security.
While I have faith that central bankers have learned much about how to handle the next crisis, their first priority will be to protect the banking system and their bosses, i.e., the government. Not investors. When the crisis hits you will hear lots of happy talk designed to calm rather than inform. One former Fed governor at the conference, Larry Meyer, concluded with these encouraging words: “Good luck–you’ll need it.”
Richard Lehmann is editor of the Forbes/Lehmann Income Securities Investor newsletter and president of Lehmann Fridson Advisors.
I’m a former Forbes columnist, investment advisor and publisher of the Forbes/Lehmann Distressed Municipal Debt Report. As a lifetime investor in postage stamps, I’ve
The “Vitruvian Man” approach to building knowledge, wisdom, and foresight.
Hemant Mohapatra on LinkedIn: “I’m taking book recommendations to.
I’m taking book recommendations to get a firmer understanding of the world at large — a sort of 101 on the fundamental…
A few weeks ago I put up a note on my LinkedIn (see above) about books that can form the building blocks to our understanding of just about everything there is to know in this universe. Essentially, I wanted to understand why are we the way we are and why have our social, political and biological systems evolved into what they are today.
The response was so good that it took me over a month to get this post together with the top 50 of the over 100+ recommendations.
I call it my “planet-scale meta-intelligence” book-list. Why planet-? To imply that all knowledge that has ever existed in the history of mankind is compressed into these 50 books. Why meta-? It certainly won’t teach you quantum mechanics or calculus — that’s too specific — but it’ll tell you why those tools were needed, when, and the part they played to get us to where we are today.
The next challenge was how to organize the list. Sure, I could fit them into history, science, psychology & influence, economics, and so on but that felt too formulaic. In thinking about how to build my intellect, I was inspired by the idea of the Vitruvian Man by Leonardo Da Vinci, who believed “the workings of the human body to be an analogy for the workings of the universe.”[ref]. Okay, Cool, Leo, but get some underwear on.
So I divided the selection into five categories:
Core: similar to working out in the gym, this part is the most important one and also the ideal starting point. Everything builds out of here. These books cover the principles of how this world works at an elemental level. A weak core makes rest of the knowledge unapproachable.
Mind: this covers how to become a better strategist, develop foresight, patience, and smarter intellectual habits. Together with the core, these two form the basics of further development IMHO.
Torso: a better upper body is often the end goal — it’s the most visible, the most outwardly attractive, and appeals to the ego. The books in this category therefore cater to matters of charisma, influence, and power.
Legs: often the most ignored part of the gym routine: leg days! Without this, your reach in the world is always going to be limited. This section covers operational experience, stories of building empires, of failures, and discipline.
Soul: finally, it’s tough to stay the course without an inspiring story or a personal passion that drives you out of bed to hit the gym. Similarly, this section focuses on feeding the soul with stories of struggles and wins against exceptional odds, stories of growth through deeply meaningful failures, and stories of redemption.
The right distribution of the topics is personal. I prefer to focus a lot more on the fundamentals: core & mind, and then divide the rest. Take it as-is but YMMV. So, without further ado, here is the list, starting with the Core. All link out to Amazon US. Again, the full list is here.
Why it is completely asinine to join as sales rep #1 : DEFCON 1–5
Morando Method: Sales Wound #143
The 2nd most common question I get asked on a weekly basis is, “Should I join a startup?”
If you’re hellbent on getting startup experience (aka joining “the $hitshow,”) hopefully it’s because you want to start your own company one day. Otherwise, stay where you are. Here are the dimensions I would use myself to evaluate the level of “$hitshow” : DEFCON 1– 5
As a baseline, let’s assume the team is strong technically and can ship code on a regular basis.
The founders have never closed an annual contract before in their career. Eject now .
Why? Closing/Shipping Revenue is just like shipping code. It’s binary, you’ve either done it or you haven’t. If you have never worked with a customer to get them to sign a piece of paper that commits them to working with you for 12 months, then I cannot begin explain how hard this is to do. It’s like explaining to your grandma what it takes to push code to Prod.
Closing an Opportunity for $10k/mo on a month2month contract where the customer can leave immediately is a 2/10 on the “difficulty of sale” scale.
Closing an Opportunity for $2k/mo for a committed, “no-outs” 12 month term is a 9/10 on the difficulty scale.
It’s not about the deal size, it’s about the time of commitment. In order to sell an annual contract at any ARR you have to sell deeper into the psychology of the buyer and higher in the org chart.
Founders “say” they understand the value of engaging with customers as an Enterprise partner. You really like their solution and you see the market opportunity.
If that’s the case then let’s experiment.
The first thing I strongly suggest founders do is to go get a contract signed. Size of the contract isn’t important. Length of the contract (12 mo) though is an absolute requirement. Only then, will you understand 20% of what it takes to be a sales pro. But you’ll have learned the single most important thing, CONTEXT.
You can work with the founders to help them qualify leads / pitch prospects / position product / close opportunities but do NOT do it for them. You’re in the background coaching them and you don’t have to be 100% on the team yet.
Typically after a founder closes the first annual contract, unassisted, the lightbulb goes off. They are beginning to learn and understand why sales is just as important as Engineering. Ship Code : Ship Revenue.
Founders have closed an annual contract. The larger the committed ACV = less risky.
But you’ll be the first sales rep hire. Roll the dice.
I’d always bet on the founders + team. If you feel you align well with them in your mindset, motivation and teamwork style then go for it. You’ll know within the first 30 days if you’ve been oversold OR you’ve oversold your skills.
Founders have closed an annual contract: AND
- There is at least 1 AE on the team
Even better as you can assess the level of experimentation the 1st AE has done. This is just an accelerator to figuring out phase 1. It’s not about how much commission the AE is making but whether the AE can close and how much assistance they need from the team. It’s ok if the founder is still on every call in the “Presales Engineer” role but that will give you a sense of how independent the AE can be based on where the product + customer fit is. getting closer to the first mini phase of repeatability.
Founders have closed an annual contract AND
- The founders have enterprise sales experience + exceptional engineering
- Engineering has had 12+ months working with real customer issues
Do whatever it takes to get onboard asap. If that means taking $0 to just get on the team to prove yourself, then do it. In 30 days they’ll be screaming to get you officially on the payroll.
Bonus: if the founders have ever worked with me before, then you’ll know that they are Defcon 5 as the first thing I advocate is the Founder needs to first close deals so they get direct context re: how difficult sales really is. No One knows how hard it is to get someone to sign a contract unless you’ve specifically done it. No One.
By Holly Hovan MSN, APRN, CWOCN-AP
A series analyzing the use of the Braden Scale for Predicting Pressure Sore Risk® in the long-term care setting. For Part 2, click here.
As wound care professionals, the Braden Scale for Predicting Pressure Sore Risk® is near and dear to our hearts. With that in mind, our evidence-based tool needs to be used correctly in order to yield accurate results. Working with long-term care and geriatric populations opens up a world of multiple pre-existing comorbidities and risk factors that aren’t always explicitly written into the Braden Scale categories. Additionally, the frequency of the Braden Scale may also contribute to a multitude of different scores; the resident behaves differently on different shifts, for example, asleep on night shift but up and about on days. What is the correct way to score them? I believe that a less frequent Braden Scale assessment yields more accurate results. However, we should still complete a Braden Scale on admission, transfer, receiving, and most importantly, with any change in condition.
What is the Braden Scale?
Briefly put, the Braden Scale is an evidenced-based tool, developed by Nancy Braden and Barbara Bergstrom, that predicts the risk for developing a hospital or facility acquired pressure ulcer/injury. The Braden Scale uses a scores from less than or equal to 9 to as high as 23. The lower the number, the higher the risk for developing an acquired ulcer/injury.
19-23 = no risk
15-18 = mild risk
13-14 = moderate risk
less than 9 = severe risk
There are six categories within the Braden Scale: sensory perception, moisture, activity, mobility, nutrition, and friction/shear.
In this blog, I will be addressing sensory perception as defined by the Braden Scale, and how this is applicable to residents of a long-term care facility.
Braden Scale Scoring for Sensory Perception
Sensory perception: the ability to respond meaningfully to pressure-related discomfort.
The resident is scored on a scale of 1-4 in the categories below:
1: Completely limited
2: Very limited
3: Slightly limited
4: No impairment
Please review the Braden Scale card for a deeper definition of each of these terms. With regard to sensory perception, I want to stress the importance of assessing neuropathy in residents with diabetes, recognizing paralysis/loss of sensation with spinal cord injury (SCI) residents, and understanding how sensory perception may vary in the dementia population.
These three populations are often seen in long-term care facilities, so it’s important to understand their unique situations. Most people recognize SCI as a loss of sensory perception, but diabetic neuropathy is sometimes missed. A simple monofilament test may be used to check for sensation/neuropathy in residents with diabetes. In addition, vascular status should be assessed, including pulses on the lower extremities and capillary refill.
After assessing for neuropathy and possibly vascular issues, the definitions of the Braden Scale for each of the subcategories (1-4) should be read and understood, and an appropriate number assigned to the subcategory. A resident with paraplegia experiencing loss of sensation to the lower half of the body would automatically only score a 2 due to loss of sensation over half of the body. A resident with diabetes with some neuropathy in the feet would automatically score a 3 if they cannot feel pain or discomfort in one or more of their extremities.
The subcategory “no impairment” is very rarely accurate with the long-term care population. These residents are in the hospital, scooting up in bed, spending more time in bed, possibly wheelchair bound, have multiple pre-existing comorbidities, and usually one or more deficits. It is possible to score a 4 here, but again, rare.
The take away point here for sensory perception is to assess for neuropathy, SCI, and dementia. These residents may often be deficient in this specific category. It is important to understand the category and definitions in order to accurately score the resident. Education with nursing staff is pertinent here, and pocket cards are always helpful. Yearly competencies for long-term care staff on Braden Scale education are also helpful, along with orientation for new nurses, to be sure that the information is understood. Education by a certified wound, ostomy and continence nurse, continued support, and follow-up are needed to ensure accurate Braden Scale scores within any facility.
Up next: The Braden Scale subcategory MOISTURE.
Note: For anyone who wishes to utilize the Braden Scale in their health care facility, you must request permission to do so. Please visit and complete the Permission Request form.
About the Author
Holly is a board certified gerontological nurse and advanced practice wound, ostomy, and continence nurse coordinator at The Department of Veterans Affairs Medical Center in Cleveland, Ohio. She has a passion for education, teaching, and our veterans. Holly has been practicing in WOC nursing for approximately six years. She has much experience with the long-term care population and chronic wounds as well as pressure injuries, diabetic ulcers, venous and arterial wounds, surgical wounds, radiation dermatitis, and wounds requiring advanced wound therapy for healing. Holly enjoys teaching new nurses about wound care and, most importantly, pressure injury prevention. She enjoys working with each patient to come up with an individualized plan of care based on their needs and overall medical situation. She values the importance of taking an interprofessional approach with wound care and prevention overall, and involves each member of the health care team as much as possible. She also values the significance of the support of leadership within her facility and the overall impact of great teamwork for positive outcomes.
The views and opinions expressed in this blog are solely those of the author, and do not represent the views of WoundSource, Kestrel Health Information, Inc., its affiliates, or subsidiary companies.
To revist this article, visit My Profile, then View saved stories.
To revist this article, visit My Profile, then View saved stories.
In the middle of the Planet Hollywood Resort & Casino convention hall in Las Vegas, amid workshops on cryptography and digital defense, a hospital will soon be humming with activity—or at least a pretty good facsimile of one. Visitors will wander through a radiology department, a pharmacy, a laboratory, and an intensive care unit. And it’ll be stocked with all the devices you’d find in a real medical center. The difference is that here, they’re supposed to get hacked.
The Medical Device Village, housed within the DefCon hacking conference BioHacking Village and opening Thursday, has previously consisted of a small table with a few medical devices available for hacking. A few FDA reps and manufacturers would talk researchers through their defenses. But as horror stories about vulnerable pacemakers or insulin pumps persist, and ransomware continues to target hospitals around the world, that more casual approach has felt increasingly insufficient. This year, it’s going all out.
“Medicine feels like one of the last industries to adopt technology in a secure, controllable way,” says Nina Alli, executive director of the BioHacking Village and a health care security researcher. “And for a long time medical device manufacturers wouldn’t come to DefCon. But they’ve become more open to working with researchers. They’re realizing that they can just get an email about a vulnerability out of the blue, or they can form relationships.”
Until very recently, most of this activity would have been not just infeasible but illegal. Medical devices only won a Digital Millennium Copyright Act exemption in 2016, allowing researchers to hack the devices without breaking the law.
Alli makes clear that previous versions of the Medical Device Village still led to some important conversations and security findings. But this year will include not just a mock hospital but also a formal capture the flag hacking competition, and much more extensive hands-on hacking. It also stresses the scope and reach of medical devices beyond high-profile implants like pacemakers. Health care environments are stuffed with sensors, scanners, monitors, and PCs that all connect to networks that share massive amounts of sensitive data. Representatives from 10 large medical device makers, including Philips Health, Medtronic, Abbott, and Becton Dickinson, will bring their expertise and insight into proprietary devices. Only a handful showed up last year.
Those companies have also thrown financial support behind the idea. DefCon doesn’t fund the villages it hosts, though it does provide space for free. After spending $5,000 to $10,000 of their own money on the Medical Device Village last year, the organizers established a nonprofit that has raised funds from medical device manufacturers and the research community for this year’s event and beyond.
“We value and support the involvement and unique perspective of independent security researchers, and appreciate their contributions to the security of our products,” says Erika Winkels, a spokesperson for Medtronic, a medical device manufacturer whose products have come under scrutiny from security researchers. “Their work helps make us better.”
This year’s village also builds on the organizers’ prior work like the Hippocratic Oath for Connected Medical Devices and a collaboration with the FDA for the village, announced in January, called We Heart Hackers. The organizers, who also include neurology researcher Sydney Swaine-Simon, independent security researcher Adrian Sanabria, and Beau Woods, a cybersafety innovation fellow at the Atlantic Council, came together in part through the grassroots computer security and human safety initiative I Am The Cavalry.
To fully grapple with the scale of the medical device security challenge, the village will be an immersive hospital setting complete with hospital rooms and a full complement of medical gadgets as you walk through. The environment, and the larger BioHacking Village, will also feature art pieces created by artists who live with or have experiences with medical devices and other biohacking.
Keyword Analysis
| Keyword | CPC | PCC | Volume | Score | Length of keyword |
|---|---|---|---|---|---|
| defcon levels explained | 0.31 | 0.5 | 9233 | 81 | 23 |
| defcon | 1.27 | 1 | 1872 | 4 | 6 |
| levels | 0.38 | 0.6 | 4815 | 50 | 6 |
| explained | 1.04 | 0.3 | 9011 | 86 | 9 |
Keyword Research: People who searched defcon levels explained also searched
| Keyword | CPC | PCC | Volume | Score |
|---|---|---|---|---|
| defcon levels explained | 0.45 | 0.5 | 5096 | 55 |
Search Results related to defcon levels explained on Search Engine
defconlevel.com
The DEFCON levels range from a scale of 1 to 5, alert level 1 the most severe warning condition status, such as a current nuclear attack or war and alert level 5 the least severe condition status and most peaceful warning level on the scale. Click on each level below to see each alert levels description.
DA: 83 PA: 39 MOZ Rank: 1
wikipedia.org
The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military. It increases in severity from DEFCON 5 (least severe) to DEFCON 1 (most severe) to match .
DA: 51 PA: 58 MOZ Rank: 18
wikihow.com
Learn how to read the DEFCON scale. The DEFCON scale is a way of assigning a numerical value to the readiness of the American military. Higher DEFCON values are used for lower levels of readiness (during more peaceful situations), while lower DEFCON values are used for higher levels of readiness (during tenser situations where the possibility of military action is more likely).
DA: 100 PA: 65 MOZ Rank: 91
explained.today
DEFCON explained. The defense readiness condition (DEFCON) is an alert state used by the United States Armed Forces.. The DEFCON system was developed by the Joint Chiefs of Staff (JCS) and unified and specified combatant commands. It prescribes five graduated levels of readiness (or states of alert) for the U.S. military.
DA: 6 PA: 77 MOZ Rank: 13
defconlevel.com
After NORAD’s creation in 1957 the first DEFCON warning alert system in history was introduced. In the beginning the defense condition system was more complex and had 3 readiness levels: normal, increased and maximum and were divided into 8 alert conditions that were later simplified.
DA: 38 PA: 63 MOZ Rank: 78
quora.com
DEFCON 1: The last thing anyone wants to happen. Nuclear war is imminent and the US armed forces is at maximum readiness around the world. Basically, the world is doomed at DEFCON 1 if it ever happens. DEFCON 2: This is the precursor to DEFCON 1 a.
DA: 12 PA: 43 MOZ Rank: 42
militarymortgagecenter.com
The DEFCON system prescribes graduated levels of readiness and states of alert and increases from levels of least to most severe. As of this moment our current military status is DEFCON 4. Defcon Levels and What They Mean. DEFCON Level 5. The normal level of peacetime readiness, DEFCON 5 serves as the baseline for the military.
DA: 11 PA: 26 MOZ Rank: 50
defconwarningsystem.com
The following are the recommended steps to take for each of the different DEFCON Warning System Alert Levels. The pubic is advised that these are only recommendations and that each individual must determine for themselves what they should do at a particular time. DEFCON 5 – Green. This is the standard peacetime alert level. All is quiet.
DA: 17 PA: 35 MOZ Rank: 65
The guidance below will help you to understand who can apply for funding, the sort of projects the Defence and Security Accelerator (DASA) funds, and the terms and conditions of DASA contracts.Who .
DA: 72 PA: 25 MOZ Rank: 42
An in-depth survey carried out amongst 100 of those attending this year’s DEFCON conference in Las Vegas recently has revealed that an overwhelming 96 percent of the respondents said they believed the cloud would open up more hacking opportunities for them.
“While ‘only’ 12 percent said they hacked cloud systems for financial gain, that still means a sizeable headache for any IT manager planning to migrate their IT resources into the cloud” said Barmak Meftah, CPO with Fortify.
According to Meftah, when you factor in the prediction from numerous analysts that at the start of 2010 20 percent of businesses would have their IT resources in the cloud within four years, you begin to appreciate the potential scale and complexity of the security issues involved.
In the many predictions, he explained, 20 per cent of organizations would own no appreciable IT assets, but would instead rely on cloud computing resources – the same resources that 45 percent of the DEFCON attendees in the survey cheerfully admitted to already having tried to hack.
Breaking down the survey responses, 21 percent believe that SaaS cloud systems are viewed as being the most vulnerable, with 33 percent of the hackers having discovered public DNS vulnerabilities, followed by log files (16 per cent) and communication profiles (12 per cent) in their cloud travels.
Remember, says Meftah, we are talking about hackers having discovered these types of vulnerabilities in the cloud, rather than merely making an observation.
| Acronym | Definition |
|---|---|
| DEFCON | Defense Readiness Condition |
| DEFCON | Defense Condition |
| DEFCON | Defence Contract Condition |
| DEFCON | Define Constant (mathematics) |
Want to thank TFD for its existence? Tell a friend about us, add a link to this page, or visit the webmaster’s page for free fun content.
Link to this page:
- ▲
- DEESMI
- DEESMT
- DEESTH
- DEESWEB
- DEET
- DEETM
- DEETS
- DEETYA
- DEEU
- DEEVAL
- DEEWR
- DEF
- DEF MAINT
- DEF-STAN
- DEFA
- DEFAC
- DEFACTO
- DEFAISE
- DEFAIT
- DEFAS
- DEFAT
- DEFB
- DEFBTN
- DEFC
- DEFCOM
- DEFCON
- DEFCON 1
- DEFCON 2-4
- DEFCON 5
- DEFCOS
- DEFD
- DEFDARS
- DEFECM
- DEFENDER
- DEFENSIVE
- DEFET
- DEFF
- DEFG
- DEFHR
- DEFI
- DEFIMNET
- DEFINTELSCOL
- DEFIS
- DEFL
- DEFLE
- DefLink
- DEFLOWH
- DEFM
- DEFMIS
- DEFN
- DEFO
- ▼
- ▲
- defaulter
- defaulter
- defaulter
- defaulter
- defaulter
- defaulters
- defaulters
- defaulters
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting
- defaulting on
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults
- defaults on
- Défauts sous Revêtement
- DEFB
- DEFBTN
- DEFC
- DEFCAP
- DEFCAP-L/S
- DEFCOM
- DEFCON
- DEFCON 1
- DEFCON 2-4
- DEFCON 5
- DEFCOS
- DEFD
- DEFDARS
- Defeasable interest
- Defeasable interest
- defeasance
- defeasance
- defeasance
- Defeasance Clause
- defeasance fee
- Defeasanced
- Defeasanced
- Defeasanced
- defeasances
- defeasances
- defeasances
- defeasibility
- defeasibility
- defeasible
- defeasible
- defeasible fee
- Defeasible reasoning
- Defeasible reasoning
- Defeasible Reasoning and Uncertainty Management Systems
- Defeasible Reasoning and Uncertainty Management Systems II
- defeasiblely
- defeasiblely
- ▼
- Facebook Share
CITE
- Terms of Use
- Privacy policy
- Feedback
- Advertise with Us
Copyright © 2003-2020 Farlex, Inc
All content on this website, including dictionary, thesaurus, literature, geography, and other reference data is for informational purposes only. This information should not be considered complete, up to date, and is not intended to be used in place of a visit, consultation, or advice of a legal, medical, or any other professional.
More Articles
- Instructions for Weight Watchers Scales
- How to Calculate How Much I’m Lifting
- How to Use a Balance Beam Scale
- Difference Between Gazelle Edge & Gazelle Freestyle
- How to Calculate BMI
A digital scales is a much more precise and uniform tool for measuring items than a manual scale. Digital scales also make measuring ingredients for recipes much easier and accurate, especially for those who are on diets and need to monitor their food intake. Digital scales come in numerous styles, however most have similar features and are generally simple to operate. Using a digital scale can seem a little confusing at first, but these steps will explain how to read a digital scale.
Follow the manufacturer’s instructions for turning the digital scale on. The scale should automatically begin with a reading of zero, reflecting that there is no weight on the scale. Set aside two quantities to be weighed for learning purposes. One should be very lightweight, such as 1/4 cup of flour and one should be a heavier weight, such as a head of lettuce.
Instructions for Weight Watchers Scales
Digital scales measure weight in units of measurement such as pounds (lbs), ounces (oz), kilograms (kg) and grams (g). Place a light object on the scale. Look at the number that is displayed on the LCD screen. Next to that number will be a unit of measurement. This gives you the weight for that specific item. For example, 10 kilograms would read 10kg.
Place a heavier item on the scale. Again, take note of the number and unit of measurement displayed on the LCD screen. For example, a head of lettuce that weighs 1 1/2 pounds will read 1.5 lbs. This is a useful tool to know when measuring out amounts for recipes.
How to Calculate How Much I’m Lifting
Digital scales also have a feature that allows you to weigh an item while it is in a container. This feature is called the tare feature. The tare feature is often used for liquids and items that cannot easily be placed directly on the scale. Use the tare feature by placing a container on the scale. Press the button that says “Tare.” This will reset the scale back to zero and will not record the weight of the container. Place the item you would like to measure into the container. The digital scale will display the weight of the item in the container not including the container itself. The tare feature will display weight on the LCD screen in the same manner as standard measurements.
Try weighing a variety of items to get used to reading the LCD display. Refer to the units of measurement in Step 2 if you are unsure of their abbreviations on the LCD. Turn the scale off when you are finished weighing.
Follow manufacturer’s instructions for advanced features.
Zscaler™ ThreatLabZ contributed to the Verizon 2019 Data Breach Investigations Report
As a society, we are more connected than ever before. Our community is no longer just the people living nearby. It is now a global community, made up of disparate individuals connected not by proximity but by the internet.
As in almost any community, crime is a factor. In today’s digital society, that means cybercriminals, and they seem to be launching new attacks every day.
These cybercriminals have gone from lone hackers to sophisticated criminal organizations, launching attacks on individuals, corporations, and governments. As these criminals have become more organized, the challenge in fighting them has become more difficult. If the cybercriminals are working together to increase their chances of success, it makes sense that those who fight these bad actors should also work together.
Today, Verizon released its 2019 Data Breach Investigations Report, and I am proud that the Zscaler ThreatLabZ team once again actively contributed to the findings in this report.
The Verizon 2019 Data Breach Investigations Report takes an in-depth look at security incidents and data breaches that occurred in 2018. The report analyzes 41,686 security incidents, of which 2,013 were confirmed data breaches. It looks at how the results have or have not changed over the years and digs into the overall threat landscape and the actors, actions, and assets that are present in breaches.
The report delves into security incident patterns and describes how they correlate to the various industry verticals. In addition to these primary patterns, the report includes a subset of data to pull out financially motivated social engineering (FMSE) attacks, which are more focused on credential theft and duping people into transferring money into adversary-controlled accounts.
Among the findings, the report revealed that 43 percent of data breaches occurred at small businesses, which tend to have less stringent security than larger organizations, making them an easier target. The most common tactic used in breaches was hacking (52 percent of the time), while errors (21 percent) and misuse by authorized users (15 percent) also led to breaches. And, as can be expected, financial gain was the most common motivation (71 percent).
These results, and the others detailed in the report, are based on data collected from a variety of sources, including publicly disclosed security incidents, cases provided by the Verizon Threat Research Advisory Center (VTRAC) investigators, and external collaborators, such as ThreatLabZ. The year-to-year data includes new sources of incident and breach data as more organizations share information to improve the diversity and coverage of real-world events.
The number of organizations providing data continues to grow, with 66 organizations external to Verizon now contributing to this report. This community of data contributors represents an international group of public and private entities that understand the importance of sharing information to gain a better understanding of the threats we all face on a daily basis.
This is the second consecutive year that Zscaler has provided transaction data for the report. The ThreatLabZ team examined transactions processed in the Zscaler cloud during 2018, specifically looking for attempted phishing attacks and blocked malware. We also offered insights into each threat category with supporting telemetry information indicating the number of users affected by these security incidents and data breaches.
It is heartening to see so many organizations coming together to share information in an ongoing effort to secure the internet and this digital world in which we all participate. Unfortunately, cybercriminals will continue developing new threats and attack methods, as long as there’s a potential payoff. And, since there is no sign of attackers stopping any time soon, it is up to all of us working in the cloud and cybersecurity industries to work together to make their job a lot more difficult.
I think Gloria Macapagal Arroyo, the 14 th President of the Philippines, said it very well: “The power of one, if fearless and focused, is formidable, but the power of many working together is better.”
Deepen Desai is vice president of security research at Zscaler